AP PGECET 2024 Computer Science Engineering Question Paper is available for download here. Sri Venkateswara University, Tirupati on behalf of APSCHE conducted AP PGECET 2024 Computer Science Engineering on May 29 in Shift 2 from 2.30 PM to 4.30 PM. AP PGECET Question Paper 2024 consists of 120 MCQ-based questions in total carrying 1 mark each to be attempted in the duration of 2 hours.
AP PGECET 2024 Computer Science Engineering Question Paper with Answer Key PDF
| AP PGECET 2024 CSE Question Paper with Answer Key | Check Solution |

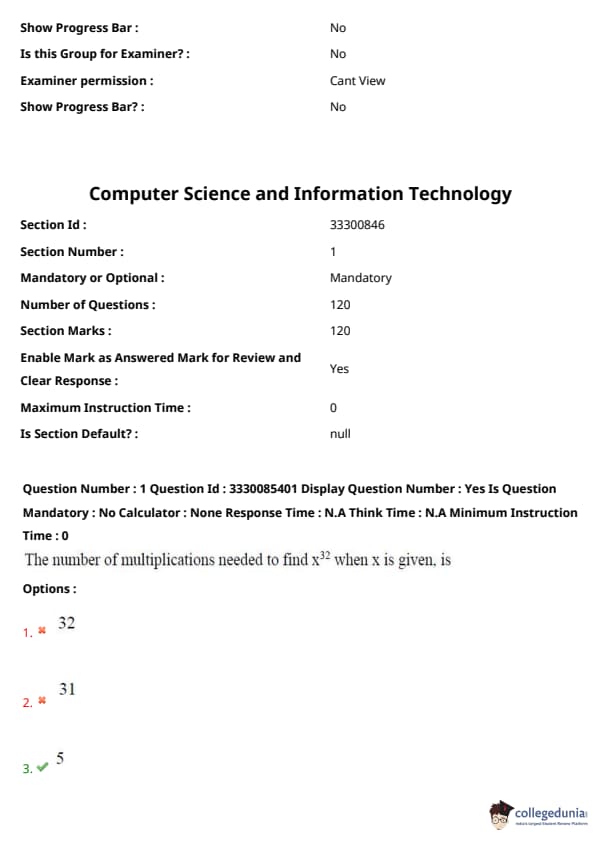
Question 1:
The number of multiplications needed to find \( x^{32} \) when \( x \) is given, is
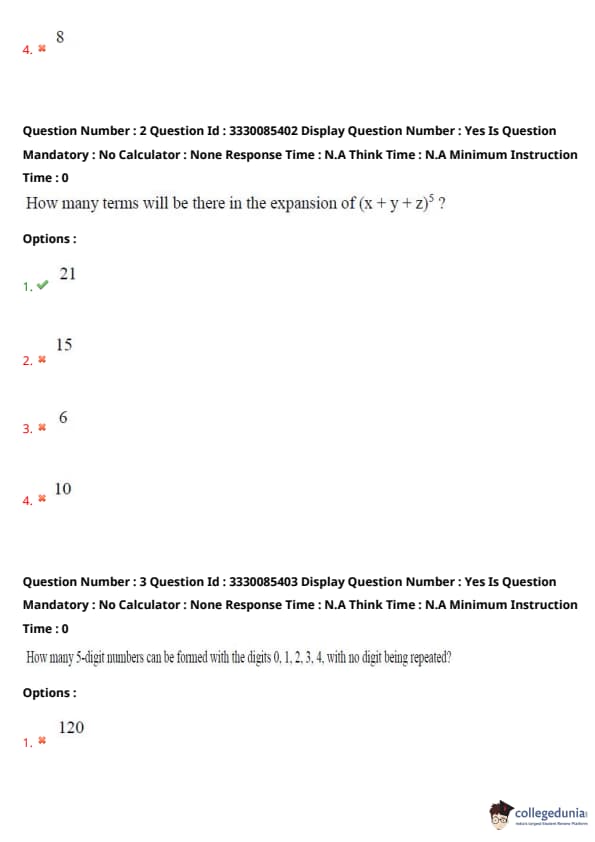
How many terms will there be in the expansion of \( (x + y + z)^5 \)?
How many 5-digit numbers can be formed with the digits 0, 1, 2, 3, 4, with no digit being repeated?
What is the generating function for \( a_r \), where \( a_r \) is the number of integral solutions for the equation \[ a + b + c = r \quad with \quad 0 \leq a, b, c \leq 3? \]
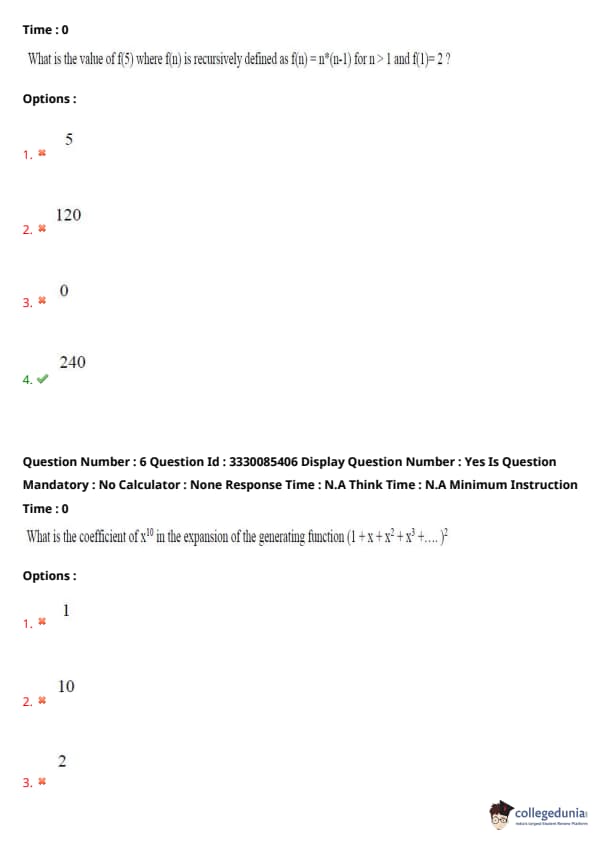
What is the value of \( f(5) \) where \( f(n) \) is recursively defined as \( f(n) = n \times (n-1) \) for \( n > 1 \) and \( f(1) = 2 \)?
What is the coefficient of \( x^{10} \) in the expansion of the generating function \[ \left( 1 + x + x^2 + x^3 + \cdots \right)^2? \]
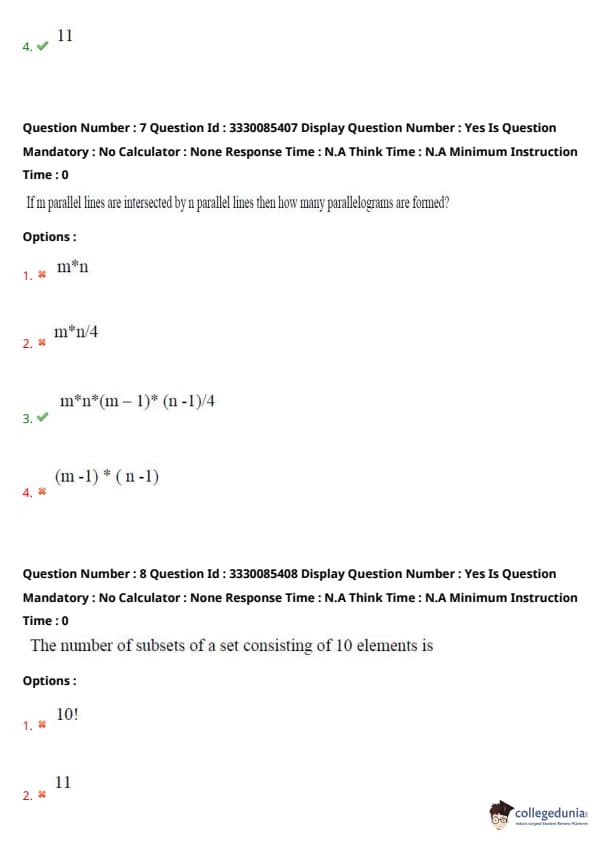
If \( m \) parallel lines are intersected by \( n \) parallel lines, then how many parallelograms are formed?
The number of subsets of a set consisting of 10 elements is?
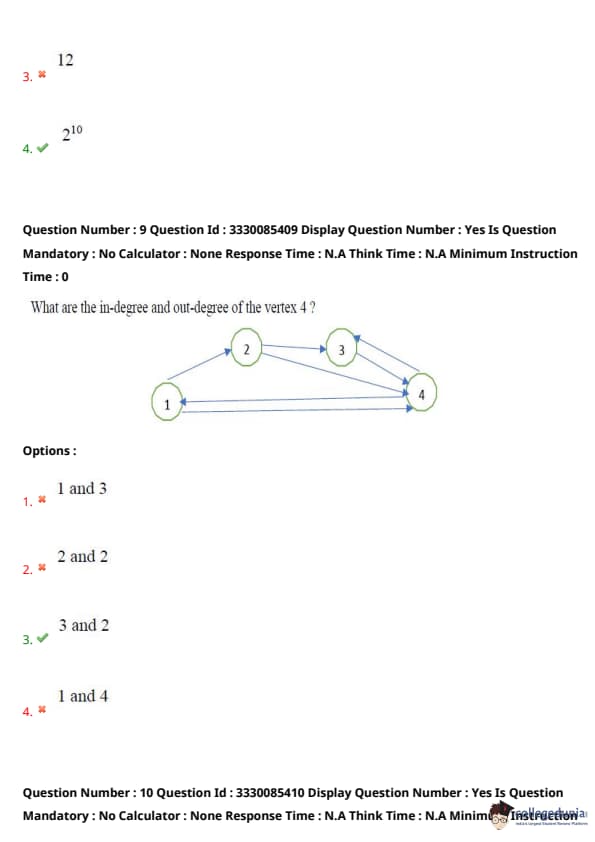
What are the in-degree and out-degree of vertex 4?
Which of the following statements is true?
A graph has \( n \) vertices and \( e \) edges. What is the number of vertices in the spanning tree of that graph?
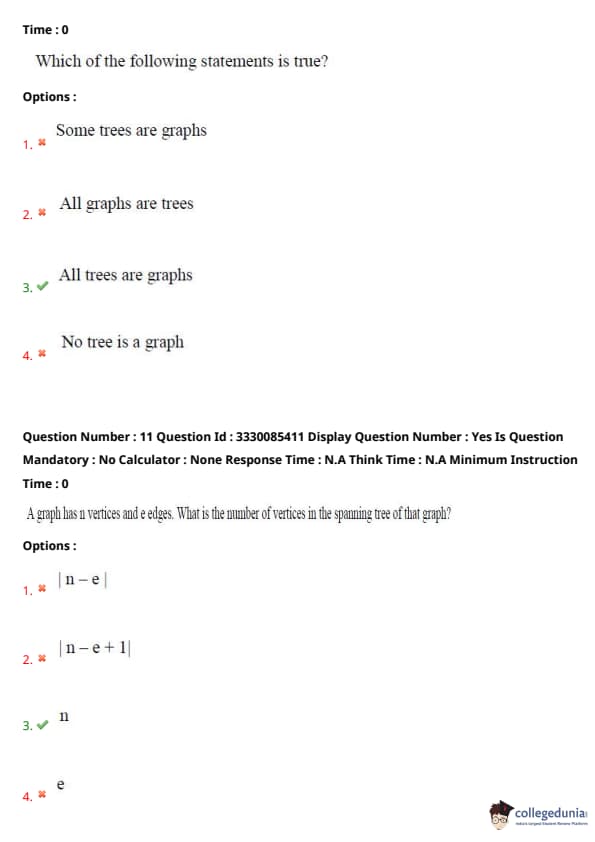
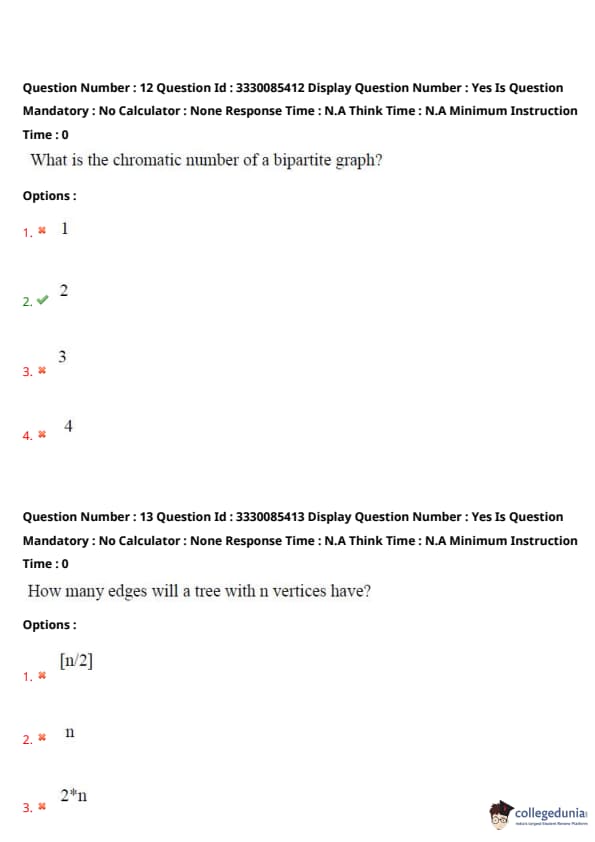
What is the chromatic number of a bipartite graph?
How many edges will a tree with \( n \) vertices have?
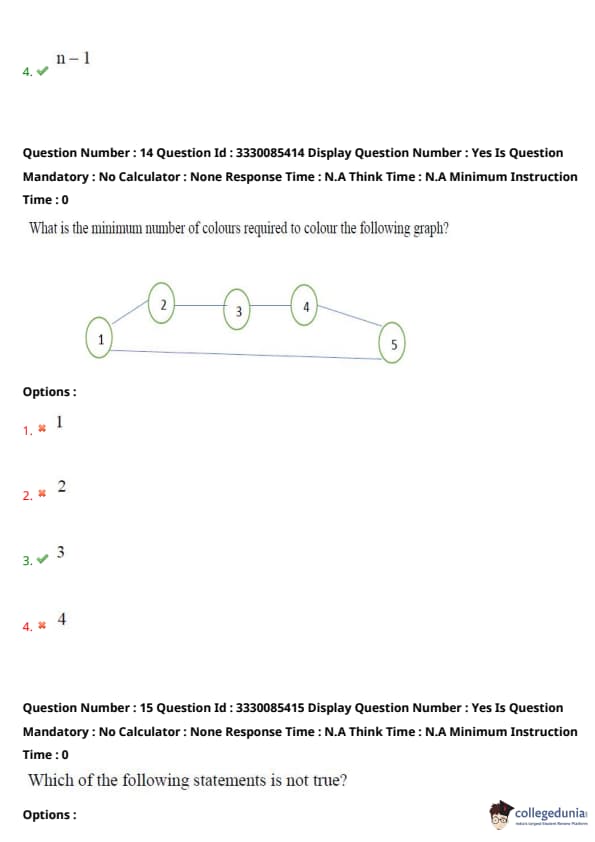
What is the minimum number of colours required to colour the following graph?
Which of the following statements is not true?
If \( P \) is false, then what is the value of the proposition \( (P \rightarrow Q) \rightarrow R \)?
The proposition \( \neg P \cup Q \) is equivalent to which of the following?
If the following four statements are presented, then which of them is true?
What is the 2's complement of 1010?
Which of the following is a tautology?
A person wishes to make up as many different parties as he can out of 50 friends. Each party consists of the same number of friends. How many should be invited at a time?
The number of 1's in the binary representation of \(13 \times 16^3 + 11 \times 16^2 + 9 \times 16 + 3\)?
A flip-flop circuit can be used for
The number of full adders in a four-bit parallel adder is
Which of the following is not a register?
The binary equivalent of \( (222)_3 \) is
The Boolean expression \( AB + AB' + AC + A'C' + AD + AD' \) is independent of which of the following variables?
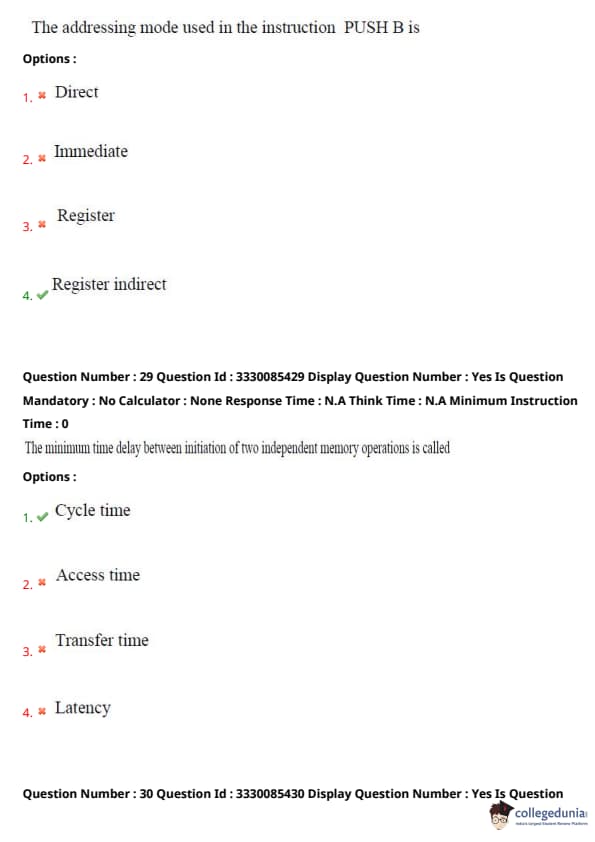
The addressing mode used in the instruction PUSH B is
The minimum time delay between initiation of two independent memory operations is called
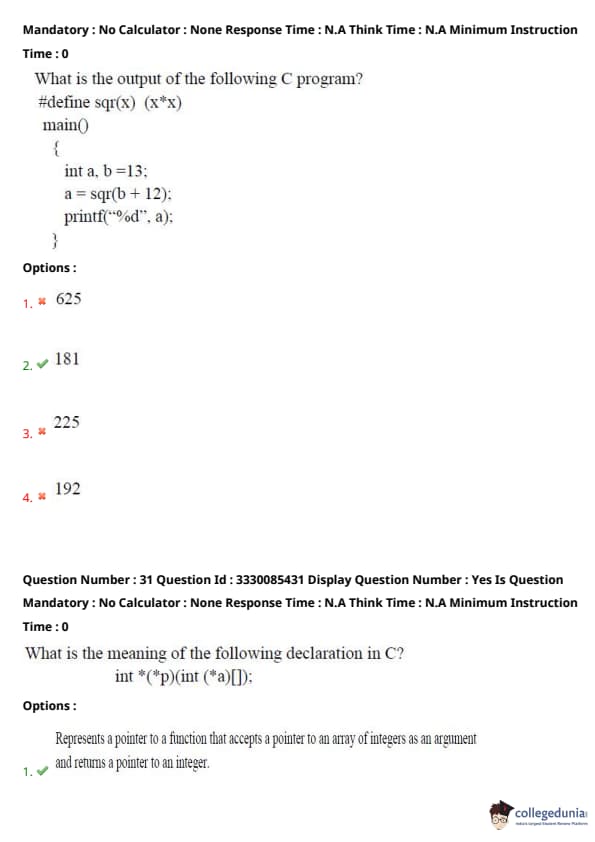
What is the output of the following C program?
#define sqr(x) (x*x)
main()
{
int a, b = 13;
a = sqr(b + 12);
printf("%d", a);
What is the meaning of the following declaration in C? \[ int *(*p)(int (*a)[]); \]
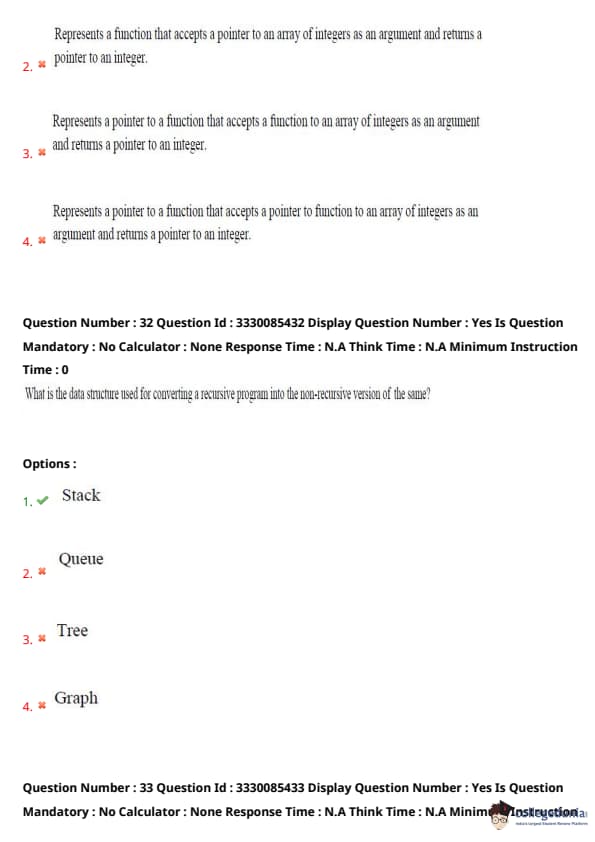
What is the data structure used for converting a recursive program into the non-recursive version of the same?
What is the value of \( x \) after the execution of the following C language statement? \[ x = -11 % -3; \]
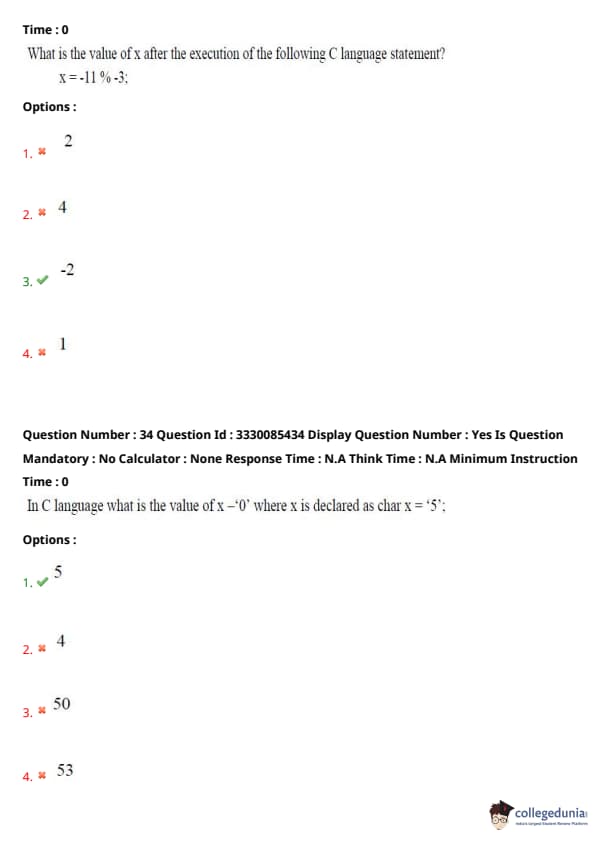
In C language, what is the value of \( x - '0' \) where \( x \) is declared as char \( x = '5'; \)?
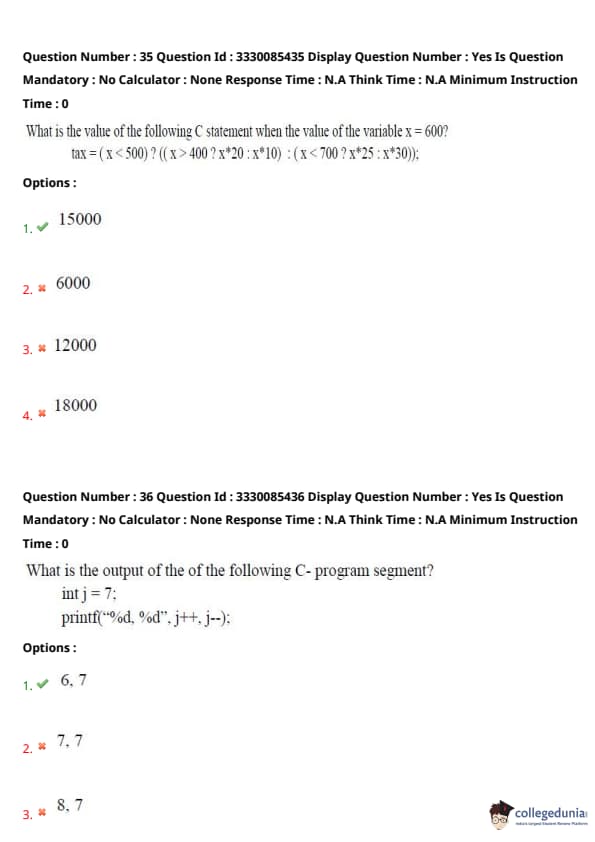
What is the value of the following C statement when the value of the variable \( x = 600 \)? \[ tax = ( x < 500 ) ? ( ( x > 400 ) ? x*20 : x*10 ) : ( x < 700 ) ? x*25 : x*30; \]
What is the output of the following C program segment? \[ int j = 7;
printf("%d, %d", j++, j--); \]
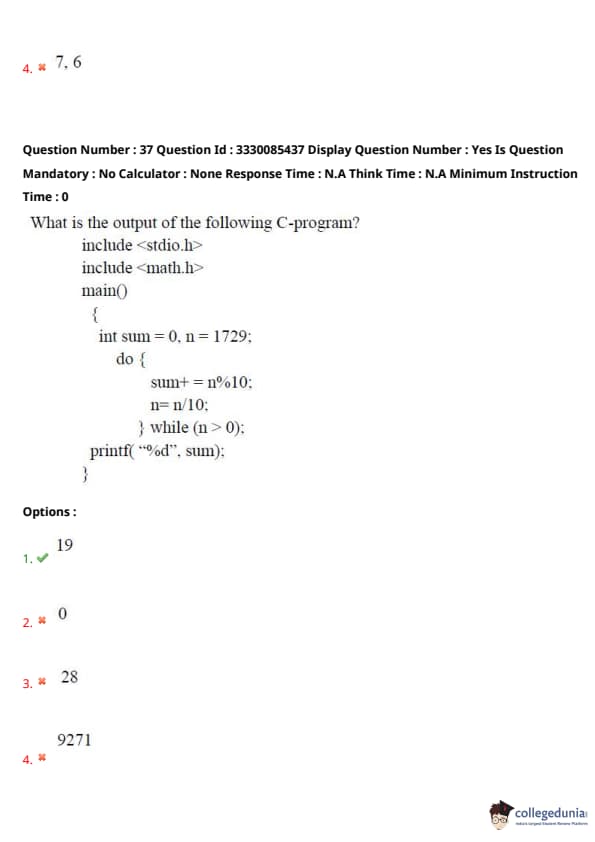
What is the output of the following C program?
#include
#include
main()
{
int sum = 0, n = 1729;
do
{
sum += n % 10;
n = n / 10;
while (n > 0);
printf("%d", sum);
How much memory is required to store the elements of the array defined as float items[4][5][6];
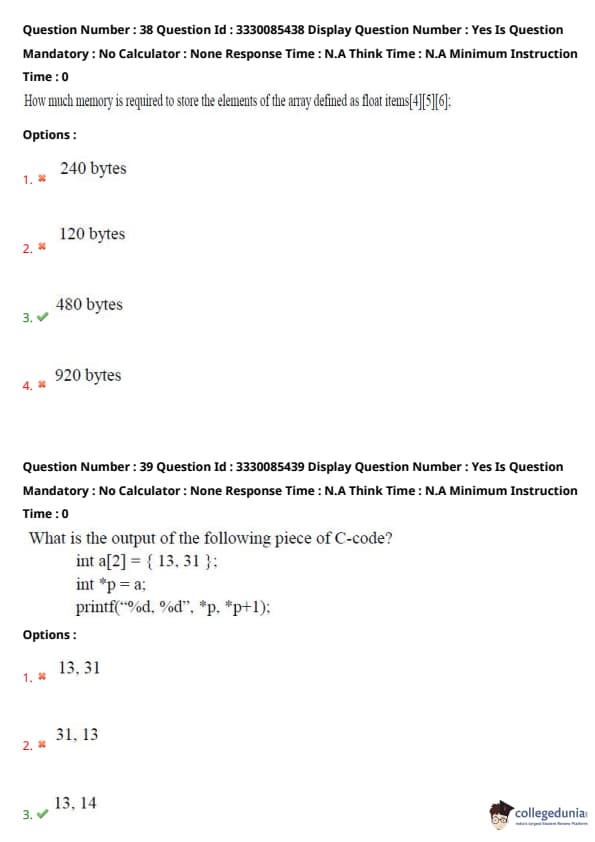
What is the output of the following piece of C code?
int a[2] = { 13, 31 ;
int *p = a;
printf("%d, %d", *p, *p++);
Which header needs to be included in C if you are to develop a function that can accept variable number of arguments?
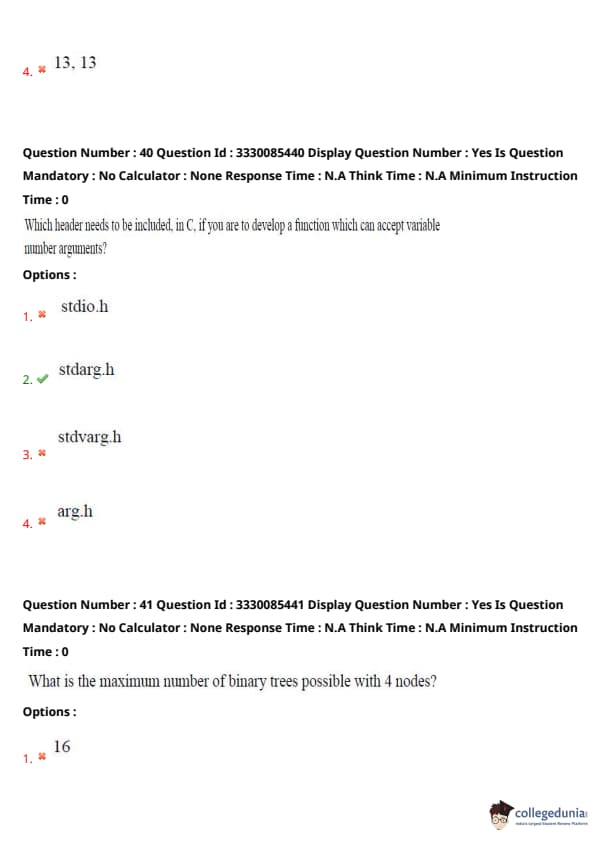
What is the maximum number of binary trees possible with 4 nodes?
The post-order traversal of a binary tree is F A E K C D H G B. What is its root?
A one-dimensional array has n elements stored from 0th position to (n-1)th position. How many elements need to be moved to insert an element at pth position of the array?
A full binary tree has n leaf nodes. How many total number of nodes will that tree have?
Which one of the following statements is true?
The average case time complexity of quick sort is
The break point of an interrupt during instruction cycle can occur at the end of
What is the relationship between clock period (\( t_c \)) and propagation delay (\( t_p \)) when a racing condition occurs in a JK flip-flop?
Which among the following consider the iterative approach to software development?
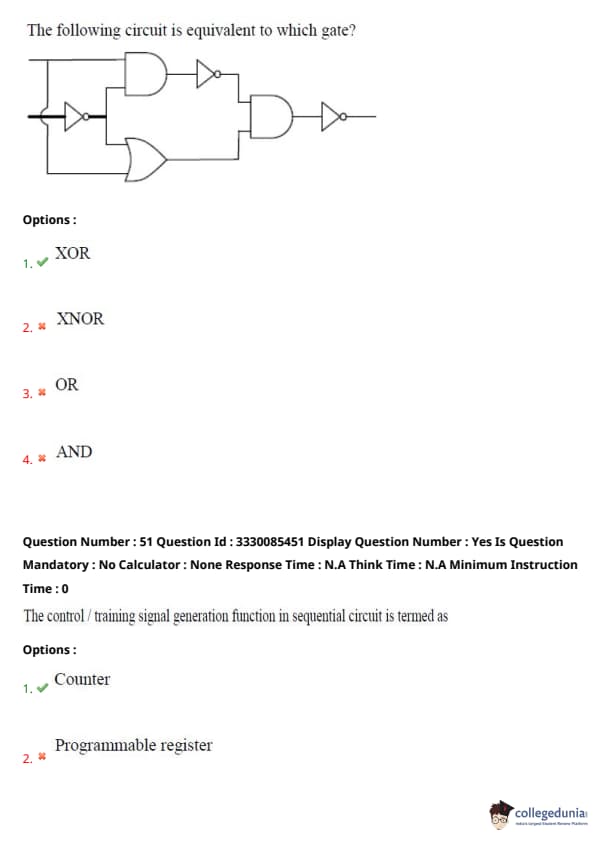
The following circuit is equivalent to which gate?
The control/training signal generation function in a sequential circuit is termed as
Which of the following problems is an example of backtracking strategy?
Which of the following is not an algorithmic strategy?
The Travelling Salesman’s is an example of which of the following class of problems?
Which of the following is an example of divide and conquer strategy?
Order the following complexities in the increasing order: \( O(n^2), O(n^3), O(\log n), O(n \log n) \)
Which of the following problems is in P?
What is the language \( L \) generated by the production rules \( SS \rightarrow aSa | bSb | a | b \) of the grammar over the alphabet \{a, b\?
A problem P is known to be NP-complete and Q and R are two problems such that Q is polynomial time reducible to P and P is polynomial time reducible to R. Which one of the following is true?
Which one of the following statements is true?
Which one of the following is not an operating system?
Which of the following is not a DBMS?
In a DBMS, a candidate which is not a primary key is called
In an RDBMS, data is represented as a set of
If a relation is in BCNF, then it is in
Referential integrity refers to which one of the following?
The concept of serializability in a database management system is related to
The method of linear probing is related to which one of the following?
The number of CODD rules which characterize an RDBMS is
Based on the following schema,
sailors (sailor-id, sailpr-name, age):
boats (boat-id, boat-name, colour):
reserves (sailor id, boat id, day);
Which of the following SQL queries returns all the ages of sailors whose names begin and end with ‘B’ and have at least three characters?
Based on the following schema,
sailors (sailor-id, sailpr-name, age):
boats (boat-id, boat-name, colour):
reserves (sailor id, boat id, day);
What does the following SQL query imply?
\texttt{SELECT S.sailor_name FROM sailors S WHERE S.sailor_id IN
\texttt{(SELECT R.sailor_id FROM reserves R WHERE R.boat_id >= 103);
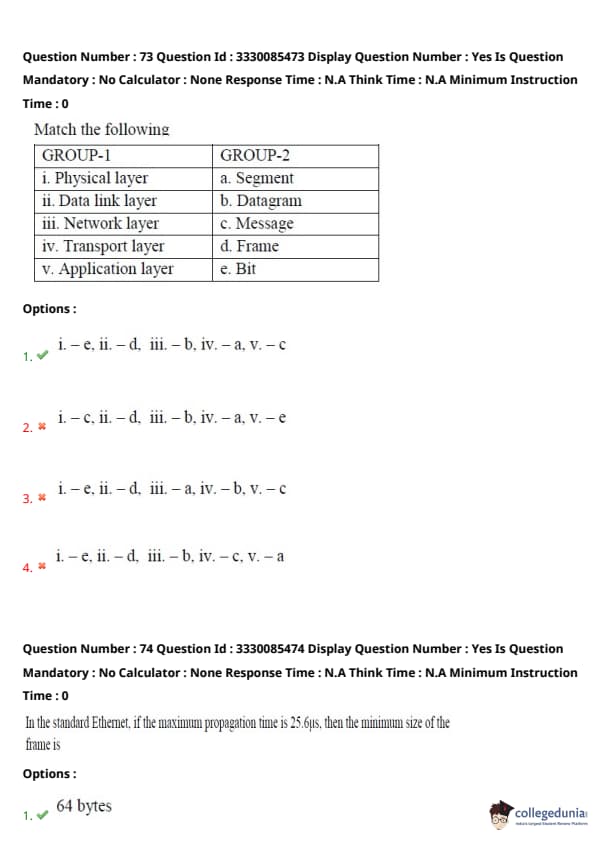
Based on the following schema,
sailors (sailor-id, sailpr-name, age):
boats (boat-id, boat-name, colour):
reserves (sailor id, boat id, day);
What does the following SQL query imply?
SELECT S.sailor_name FROM sailors S, boats B, reserves R
WHERE S.sailor_id = R.sailor_id AND R.boat_id = B.boat_id
AND (B.colour = 'red' OR B.colour = 'green');
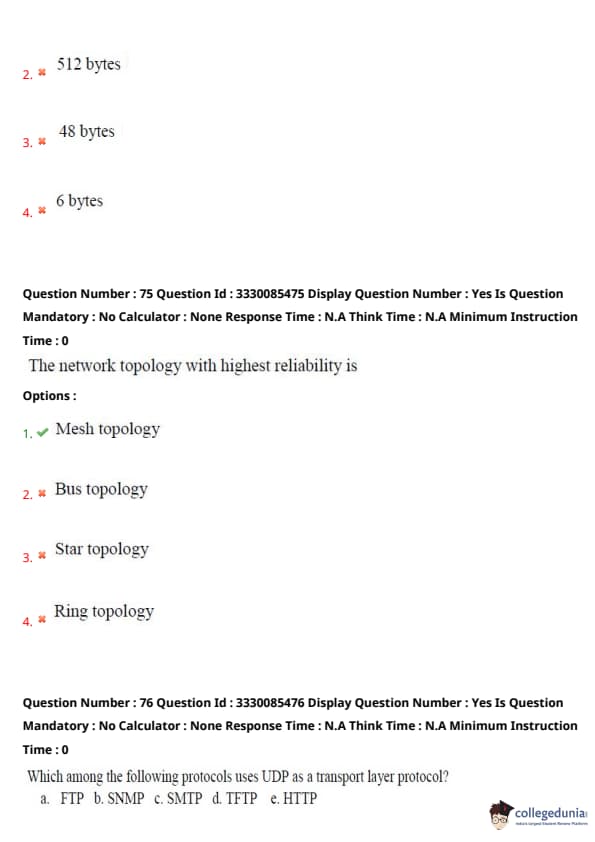
Match the following:
Group-1 Layer Group-2 (Corresponding Unit)
i. Physical layer e. Bit
ii. Data link layer d. Frame
iii. Network layer b. Datagram
iv. Transport layer a. Segment
v. Application layer c. Message
View Solution
Let us match each layer from Group-1 to its corresponding data unit in Group-2:
% Option
(A) Physical layer uses transmission units of individual bits: \(\Rightarrow\) e. Bit
% Option
(B) Data Link layer works with frames for error detection and framing: \(\Rightarrow\) d. Frame
% Option
(C) Network layer handles packets, often called datagrams: \(\Rightarrow\) b. Datagram
% Option
(D) Transport layer manages segments in protocols like TCP: \(\Rightarrow\) a. Segment
% Option
(E) Application layer deals with complete messages as seen by applications: \(\Rightarrow\) (3) Message
%Quicktip Quick Tip: In networking, different layers handle different data units — remember the order: Bit → Frame → Datagram → Segment → Message (from Physical to Application layer).
In the standard Ethernet, if the maximum propagation time is 25.6 µs, then the minimum size of the frame is
The network topology with highest reliability is
Which among the following protocols uses UDP as a transport layer protocol?
a. FTP b. SNMP c. SMTP d. TFTP e. HTTP
End to end connectivity is provided from host to host in which one of the following layers?
The Hamming distance between 11001011 and 10000111 is
View Solution
To verify a digital signature, we need the ..........
Maximum data rate of a channel for noiseless 3 kHz binary channel is
Which of the following is not a web component element?
Which one of the following is commonly used for server side scripting in web development?
Statement 1: When dynamic programming is applied to a problem, it takes far less time as compared to other methods that don't take advantage of overlapping subproblems.
Statement 2: A greedy algorithm can be used to solve all the dynamic programming problems.
What does \
Which font format is used in web pages?
Telnet is
A computer has 24-bit address bus and an instruction format providing 12 bits in the address part. What is the maximum addressable range?
In a page segmented system, a virtual address consists of 32 bits of which 12 bits are a displacement, 11 bits are segment number, and 9 bits are page number. What is the page size?
Which of the following is essential for converting an infix expression to the postfix form efficiently?
What do semaphores do?
The memory allocation scheme subject to external fragmentation is
Which one of the following is related to deadlock?
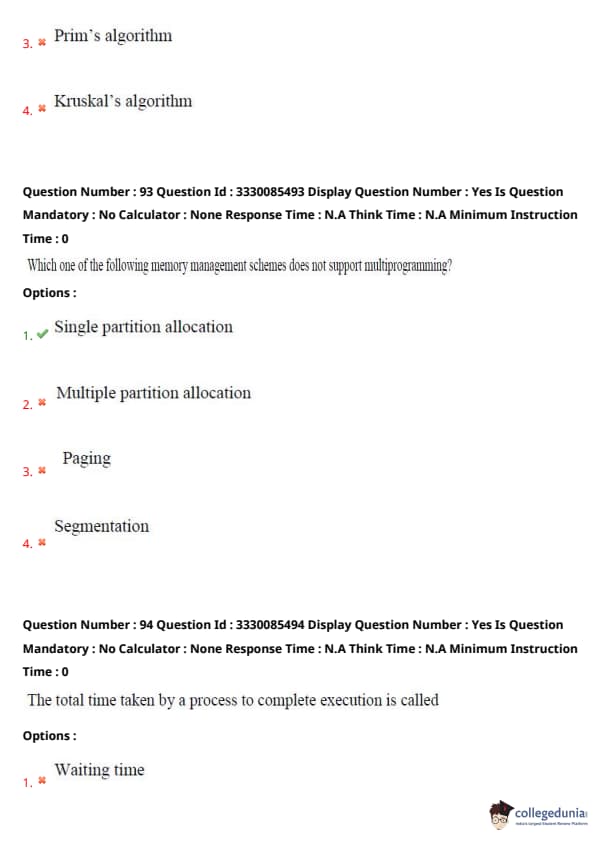
Which one of the following memory management schemes does not support multiprogramming?
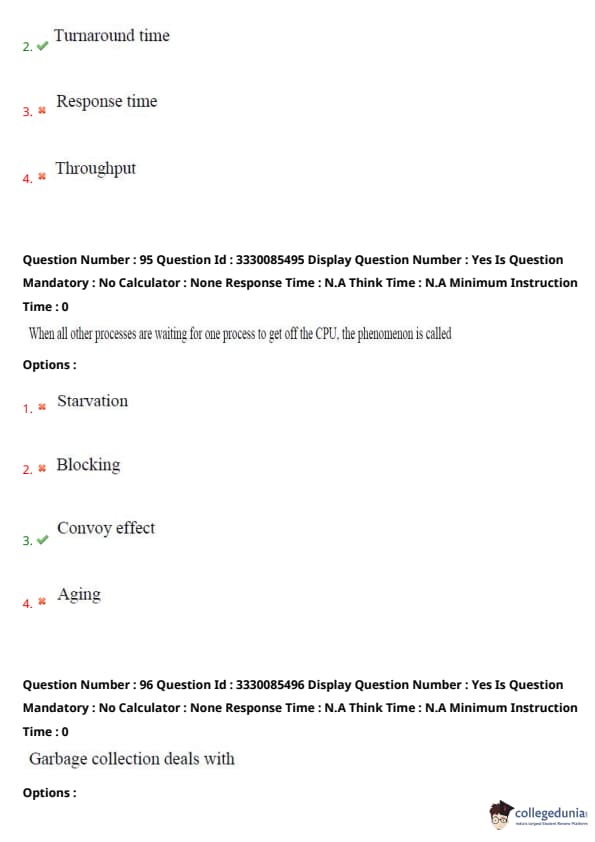
The total time taken by a process to complete execution is called
When all other processes are waiting for one process to get off the CPU, the phenomenon is called
Garbage collection deals with
The term cyclomatic complexity is related to
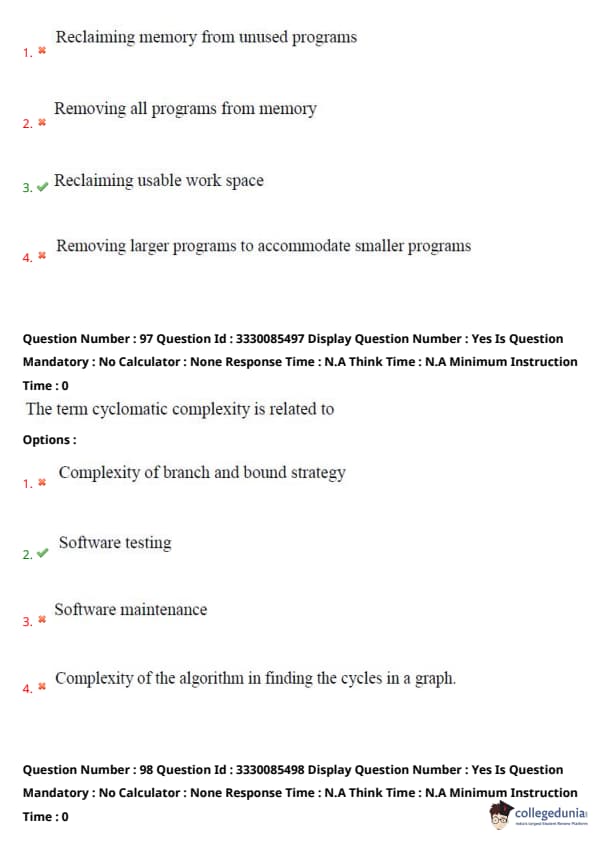
Assume transaction A holds a shared lock R. If transaction B also requests for a shared lock on R, it will
View Solution
- **Option 1**: The shared lock is not rejected as both transactions are requesting read access (shared locks), so there is no conflict.
- **Option 2**: There is no deadlock situation in this scenario. Deadlocks usually happen when one transaction is waiting for a resource held by another transaction in an incompatible mode (like exclusive locks).
- **Option 3**: Shared locks are not immediately rejected. Multiple transactions can hold shared locks on the same resource.
- **Option 4**: This is correct. A shared lock allows other transactions to request shared locks on the resource, and it will be granted once transaction A releases the lock.
Therefore, the correct answer is (4) Be granted as soon as it is released by A. Quick Tip: Shared locks allow multiple transactions to read the same resource concurrently, but any exclusive lock or write operation is not allowed until all shared locks are released.
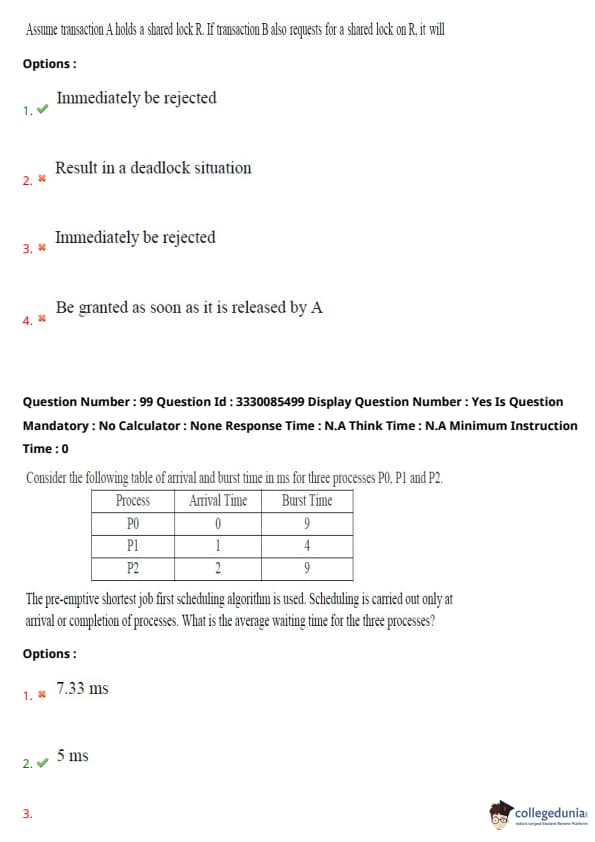
Consider the following table of arrival and burst time in ms for three processes P0, P1, and P(2)
Process Arrival Time Burst Time
P0 0 9
P1 1 4
P2 2 9
The preemptive shortest job first scheduling algorithm is used. Scheduling is carried out only at arrival or completion of processes. What is the average waiting time for the three processes?
View Solution
The preemptive shortest job first (SJF) scheduling algorithm works by selecting the process with the shortest burst time from the ready queue. Let's calculate the average waiting time:
% Option
(1) **At time 0**, process P0 arrives with a burst time of 9 ms.
% Option
(2) **At time 1**, process P1 arrives with a burst time of 4 ms, so it preempts P0.
% Option
(3) **At time 2**, process P2 arrives with a burst time of 9 ms, but since P1 has the shortest burst time, P1 continues executing.
% Option
(4) **P1 finishes** at time 5, and process P0, which has the next shortest burst time (9 ms), resumes.
5. **P0 executes** from time 5 to 9 and completes.
6. **P2** starts executing at time 9 and finishes at time 18.
Now, calculate the waiting time for each process:
- **Waiting time for P0**: It started at time 5 and finished at time 9. So, waiting time = (start time - arrival time) = 5 - 0 = 5 ms.
- **Waiting time for P1**: It started at time 1 and finished at time 5. So, waiting time = (start time - arrival time) = 1 - 1 = 0 ms.
- **Waiting time for P2**: It started at time 9 and finished at time 18. So, waiting time = (start time - arrival time) = 9 - 2 = 7 ms.
The average waiting time is calculated as: \[ Average Waiting Time = \frac{5 + 0 + 7}{3} = 5 \, ms \]
Therefore, the correct answer is (2) 5 ms. Quick Tip: The preemptive SJF scheduling algorithm selects the process with the shortest burst time. Calculate the waiting time by subtracting the arrival time from the start time for each process.
In a particular bank, a loan can belong to only one customer and a customer can have several loans. Then the relationship from customer to loans is
View Solution
- **One to many**: This is the correct answer because each customer can have several loans, but each loan belongs to only one customer. Hence, the relationship is one-to-many.
- **Many to many**: This is incorrect because each loan belongs to exactly one customer, not multiple customers.
- **Many to one**: This is incorrect because a customer can have multiple loans, not just one.
- **One to one**: This is incorrect because a customer can have several loans, not just one.
Therefore, the correct answer is (4) One to many. Quick Tip: In a one-to-many relationship, one entity (in this case, the customer) can be associated with multiple instances of another entity (the loans).
The number of binary relations on a set with 3 elements is
View Solution
The number of binary relations on a set with \(n\) elements is given by \( 2^{n^2} \). For a set with 3 elements, the calculation is:
\[ 2^{3^2} = 2^9 = 512 \]
Therefore, the correct answer is (3) 51(2) Quick Tip: The number of binary relations on a set of \(n\) elements is \( 2^{n^2} \), as each pair of elements can either have a relation or not.
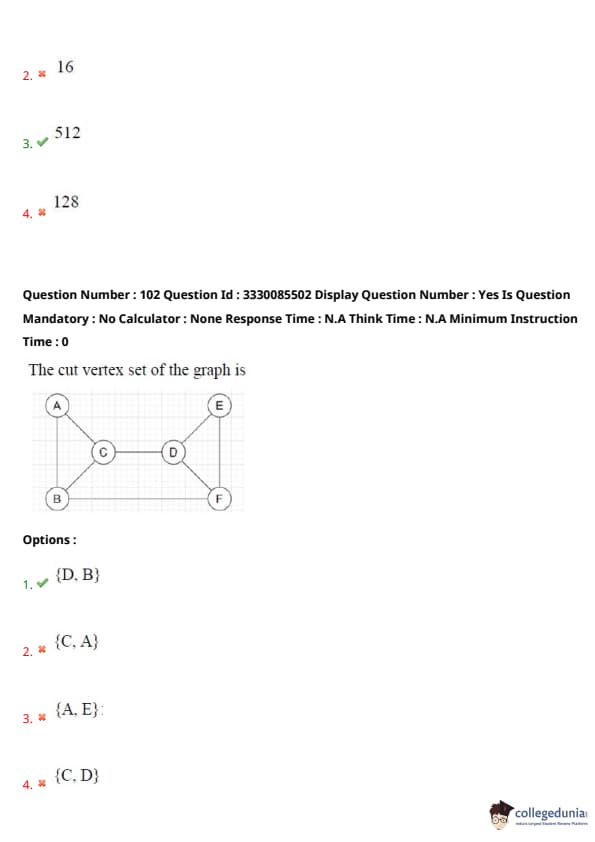
The cut vertex set of the graph is
View Solution
A **cut vertex** is a vertex whose removal results in increasing the number of connected components in a graph. In this graph, removing **D** or **B** disconnects the graph. Therefore, **D** and **B** are the cut vertices.
Thus, the correct answer is **(1) \{D, B\**. Quick Tip: Cut vertices (articulation points) are critical for the connectivity of a graph. Removing them can split the graph into separate components.
Register A holds the 8-bit binary 1101100(1) To change the value of Register A to 01101101, the following logic microoperation has to be performed on the operand respectively.
View Solution
The initial value of Register A is 11011001, and we want to change it to 0110110(1) To achieve this, we perform a bitwise XOR operation with a mask. The mask that will flip the necessary bits is **10110100**.
\[ 11011001 \, XOR \, 10110100 = 01101101 \]
Thus, performing XOR with the mask **10110100** changes the value of Register A to 0110110(1)
Therefore, the correct answer is (1) 10110100, XOR. Quick Tip: XOR (exclusive OR) is used to flip specific bits where the mask has 1s, and leave others unchanged. It is commonly used in bit manipulation tasks.
The number of clock cycles that it takes to process 200 tasks in a six-segment pipeline is
View Solution
In a pipelined system with **m** stages, the number of clock cycles required to process **n** tasks is given by the formula:
\[ Total clock cycles = (n + m - 1) \]
Where:
- **n** = 200 (number of tasks)
- **m** = 6 (number of segments in the pipeline)
Thus, the total clock cycles is:
\[ Total clock cycles = 200 + 6 - 1 = 205 \]
Therefore, the correct answer is **(1) 205**. Quick Tip: The number of clock cycles required to process tasks in a pipelined system depends on the number of stages and the total number of tasks.
Which of the following is related to DBMS?
View Solution
- **Public key**: A public key is used in cryptography for secure communication but is not directly related to DBMS.
- **Private key**: A private key is also a cryptographic concept and is not associated with DBMS concepts.
- **Symmetric key**: Symmetric key encryption is a cryptographic concept and is not directly related to DBMS.
- **Candidate key**: In the context of a DBMS, a candidate key is a set of attributes that uniquely identifies a record in a relation (table). It is a core concept of database design.
Therefore, the correct answer is **(4) Candidate key**. Quick Tip: A candidate key in a relational database is a set of one or more columns that can uniquely identify a row in a table. A primary key is selected from the candidate keys.
The set \( S = \{1, 2, 3, 4, 5, 6, 7, 8, 9, 10, 11, 12\} \) is to be partitioned into three sets \( A, B, C \) of equal size. Thus \( A \cup B \cup C = S \), \( A \cap B = B \cap C = A \cap C = \emptyset \). The number of ways to partition \( S \) is
View Solution
We need to partition a set of 12 elements into three subsets \( A \), \( B \), and \( C \), each containing 4 elements. The total number of ways to do this is given by:
\[ \frac{12!}{(4!)^3 \times 3!} \]
However, the correct expression for the number of ways to partition the set is already simplified in the options as:
\[ \frac{12!}{(4!)^3} \]
Therefore, the correct answer is **(1) \( \frac{12!}{(4!)^3} \)**. Quick Tip: The formula for partitioning a set of \( n \) elements into subsets of equal size \( k \) is \( \frac{n!}{(k!)^m \times m!} \), where \( m \) is the number of subsets.
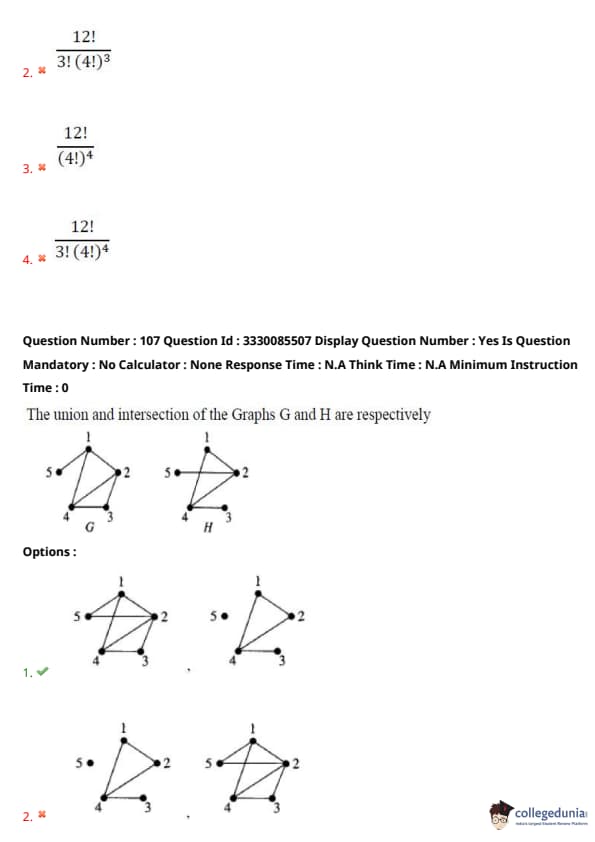
The union and intersection of the graphs G and H are respectively
View Solution
To find the **union** of two graphs, we combine the vertices and edges of both graphs.
To find the **intersection**, we retain only the vertices and edges that are common to both graphs.
Thus, the correct answer is the graph with the union and intersection of \( G \) and \( H \), as shown in **Option 1**. Quick Tip: The union of two graphs includes all vertices and edges from both graphs, while the intersection includes only those that are common to both graphs.
Match the following:
GROUP-I GROUP-II
a. Lexical Analysis i. Shift-reduce
b. Syntax Analysis ii. Scanner
c. Generate code for multiple machines iii. Parser
d. Bottom-up parsing iv. Cross Compiler
View Solution
- **Lexical Analysis** corresponds to **Scanner (ii)** as it scans the source code for tokens.
- **Syntax Analysis** corresponds to **Parser (iii)** as it parses the tokens into a syntax tree.
- **Generate code for multiple machines** corresponds to **Cross Compiler (iv)**, which generates code for different machine architectures.
- **Bottom-up parsing** corresponds to **Shift-reduce (i)** as a type of parsing in bottom-up methods.
Therefore, the correct answer is **(1) a – ii, b – iii, c – iv, d – i**. Quick Tip: Lexical analysis, syntax analysis, and code generation are fundamental phases in a compiler, and understanding their connections helps in solving matching questions like this one.
Let \( A \) and \( B \) be two independent events, then \( P(A \cap B') = \)
View Solution
For two independent events \( A \) and \( B \), the probability of their intersection with the complement of \( B \) is:
\[ P(A \cap B') = P(A) \cdot P(B') \]
This follows from the independence of \( A \) and \( B \), meaning the occurrence of one does not affect the probability of the other.
Therefore, the correct answer is **(1) \( P(A) \cdot P(B') \)**. Quick Tip: For independent events, the probability of the intersection of an event and the complement of another event is the product of the probabilities of the events.
A pair of dice is thrown. The probability that the sum is neither 7 nor 8 is
View Solution
When two dice are thrown, there are a total of \( 6 \times 6 = 36 \) possible outcomes.
- The sum of **7** can be obtained in the following combinations: (1, 6), (2, 5), (3, 4), (4, 3), (5, 2), (6, 1) — **6 outcomes**.
- The sum of **8** can be obtained in the following combinations: (2, 6), (3, 5), (4, 4), (5, 3), (6, 2) — **5 outcomes**.
Thus, the total number of outcomes where the sum is 7 or 8 is \( 6 + 5 = 11 \).
The probability that the sum is neither 7 nor 8 is:
\[ \frac{36 - 11}{36} = \frac{25}{36} \]
Therefore, the correct answer is **(4) \( \frac{25}{36} \)**. Quick Tip: When calculating probabilities involving dice rolls, count the outcomes for the desired sums, then subtract from the total number of possible outcomes to find the complementary probability.
Let \( X \) be a continuous random variable denoting the temperature measured. The range of temperature is \( [0, 100] \) degrees Celsius and let the probability density function of \( X \) be \( f(X) = 0.01 \) for \( 0 \leq X \leq 100 \). The mean is
View Solution
The probability density function \( f(X) = 0.01 \) represents a uniform distribution over the interval \( [0, 100] \). The mean of a uniform distribution is given by:
\[ Mean = \frac{a + b}{2} \]
Where \( a = 0 \) and \( b = 100 \). Therefore:
\[ Mean = \frac{0 + 100}{2} = 50 \]
Thus, the correct answer is **(4) 50.0**. Quick Tip: For a uniform distribution, the mean is simply the average of the lower and upper bounds of the distribution.
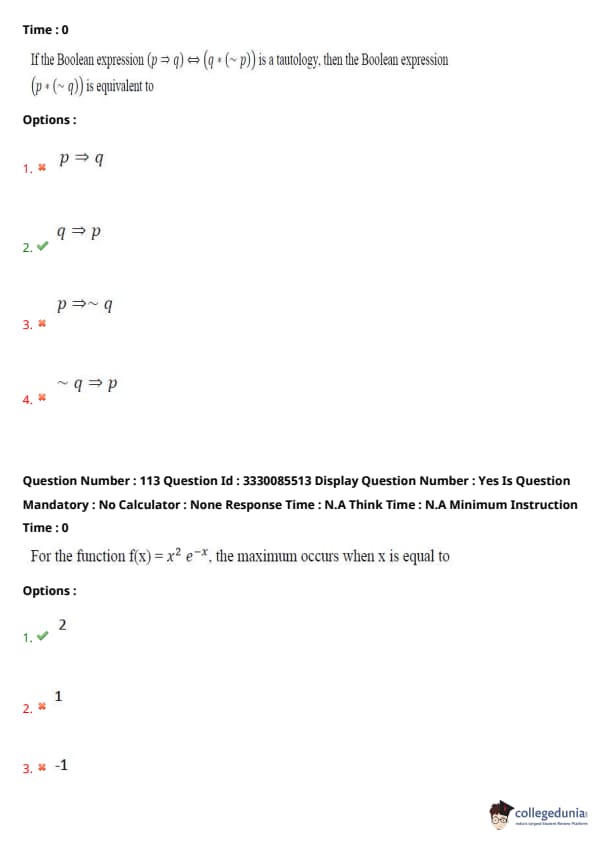
If the Boolean expression \( (p \Rightarrow q) \Leftrightarrow (q \land (\sim p)) \) is a tautology, then the Boolean expression \( (p \land (\sim q)) \) is equivalent to
View Solution
We are given that the Boolean expression \( (p \Rightarrow q) \Leftrightarrow (q \land (\sim p)) \) is a tautology. This condition means that the truth values of both sides of the equivalence must always be the same.
By simplifying the tautology, we deduce the relationship between \( p \) and \( q \). For the expression \( (p \land (\sim q)) \), it is equivalent to the logical implication \( q \Rightarrow p \), as this is the expression that satisfies the given tautology condition.
Therefore, the correct answer is **(2) \( q \Rightarrow p \)**. Quick Tip: Tautologies often help us find relationships between variables. Here, simplifying the expression helps us deduce the correct equivalence for the given Boolean expression.
For the function \( f(x) = x^2 e^{-x} \), the maximum occurs when \( x \) is equal to
View Solution
To find the value of \( x \) where the function \( f(x) = x^2 e^{-x} \) attains its maximum, we first need to take the derivative of the function with respect to \( x \), set it equal to zero, and solve for \( x \).
First, compute the derivative of \( f(x) \):
\[ f'(x) = \frac{d}{dx} \left( x^2 e^{-x} \right) \]
Using the product rule:
\[ f'(x) = 2x e^{-x} - x^2 e^{-x} \]
Simplifying:
\[ f'(x) = e^{-x} (2x - x^2) \]
To find the critical points, set \( f'(x) = 0 \):
\[ e^{-x} (2x - x^2) = 0 \]
Since \( e^{-x} \neq 0 \) for any real value of \( x \), we solve:
\[ 2x - x^2 = 0 \]
\[ x(2 - x) = 0 \]
This gives \( x = 0 \) or \( x = 2 \).
By applying the second derivative test or analyzing the first derivative, it can be shown that the function reaches its maximum at \( x = 2 \).
Therefore, the correct answer is **(1) 2**. Quick Tip: To find the maximum or minimum of a function, take its derivative, set it to zero, and solve for \( x \). Check the second derivative to confirm if it's a maximum or minimum.
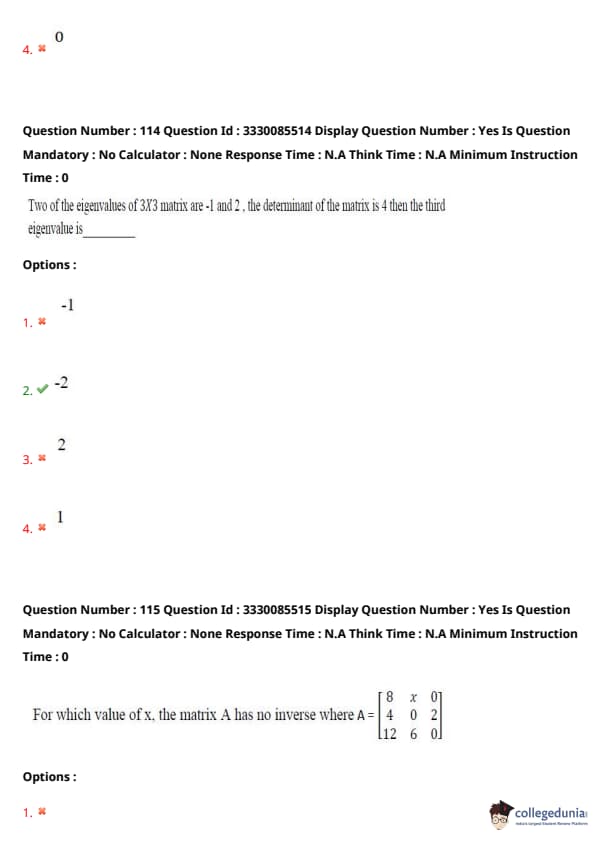
Two of the eigenvalues of a 3x3 matrix are -1 and (2) The determinant of the matrix is (4) Then the third eigenvalue is
View Solution
The determinant of a matrix is the product of its eigenvalues. For a 3x3 matrix with eigenvalues \( \lambda_1 \), \( \lambda_2 \), and \( \lambda_3 \), we have:
\[ det(A) = \lambda_1 \cdot \lambda_2 \cdot \lambda_3 \]
Given that \( \lambda_1 = -1 \), \( \lambda_2 = 2 \), and \( det(A) = 4 \), we substitute into the equation:
\[ 4 = (-1) \cdot 2 \cdot \lambda_3 \]
Solving for \( \lambda_3 \):
\[ \lambda_3 = \frac{4}{-1 \cdot 2} = \frac{4}{-2} = -2 \]
Therefore, the third eigenvalue is **-2**. Quick Tip: The determinant of a matrix is the product of its eigenvalues. If you know the determinant and some eigenvalues, you can solve for the remaining eigenvalues.
For which value of \( x \), the matrix \( A \) has no inverse where
\[ A = \begin{pmatrix} 8 & x & 0
4 & 0 & 2
12 & 6 & 0 \end{pmatrix} \]
View Solution
The matrix \( A \) has no inverse if its determinant is zero. To find the determinant of \( A \), we calculate:
\[ det(A) = \begin{vmatrix} 8 & x & 0
4 & 0 & 2
12 & 6 & 0 \end{vmatrix} \]
Using cofactor expansion along the first row:
\[ det(A) = 8 \begin{vmatrix} 0 & 2
6 & 0 \end{vmatrix} - x \begin{vmatrix} 4 & 2
12 & 0 \end{vmatrix} + 0 \]
Now, calculate the 2x2 determinants:
\[ \begin{vmatrix} 0 & 2
6 & 0 \end{vmatrix} = -12 \]
\[ \begin{vmatrix} 4 & 2
12 & 0 \end{vmatrix} = -24 \]
Thus, we get:
\[ det(A) = 8 \cdot (-12) - x \cdot (-24) = -96 + 24x \]
For the matrix to have no inverse, we set the determinant equal to zero:
\[ -96 + 24x = 0 \]
Solving for \( x \):
\[ 24x = 96 \]
\[ x = 4 \]
Therefore, the correct answer is **(2) 4**. Quick Tip: A matrix has no inverse if and only if its determinant is zero. Always calculate the determinant to check for invertibility.
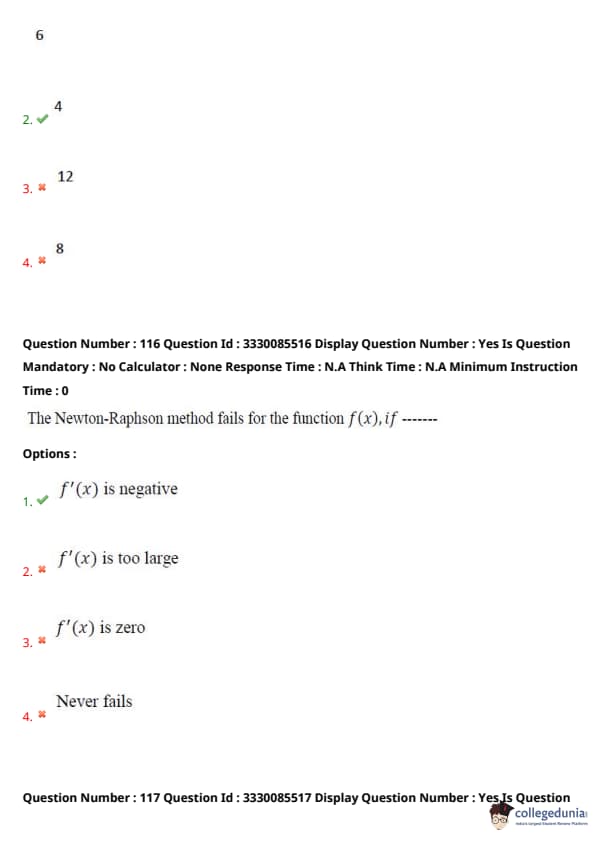
The Newton-Raphson method fails for the function \( f(x) \), if
View Solution
The Newton-Raphson method is an iterative method used to find the roots of a function. The formula is:
\[ x_{n+1} = x_n - \frac{f(x_n)}{f'(x_n)} \]
For the method to work, \( f'(x_n) \) must not be zero. If \( f'(x) = 0 \), the method fails because division by zero is undefined.
Therefore, the correct answer is **(3) \( f'(x) \) is zero**. Quick Tip: Always check the derivative when applying the Newton-Raphson method. If the derivative is zero at any point, the method cannot be used at that point.
The quadratic equation \( 2x^2 - 3x + 3 = 0 \) is to be solved numerically starting with initial guess \( x_0 = 2 \). The new estimate of \( x \) after the first iteration using the Newton-Raphson method is
View Solution
The Newton-Raphson method is used to find the roots of a function. The iterative formula for the Newton-Raphson method is:
\[ x_{n+1} = x_n - \frac{f(x_n)}{f'(x_n)} \]
Given the equation \( f(x) = 2x^2 - 3x + 3 \), we need to first compute \( f(x) \) and its derivative \( f'(x) \):
\[ f(x) = 2x^2 - 3x + 3 \]
\[ f'(x) = 4x - 3 \]
Now, substitute the initial guess \( x_0 = 2 \) into the formula:
\[ f(2) = 2(2)^2 - 3(2) + 3 = 8 - 6 + 3 = 5 \]
\[ f'(2) = 4(2) - 3 = 8 - 3 = 5 \]
Now, using the Newton-Raphson formula:
\[ x_1 = 2 - \frac{5}{5} = 2 - 1 = 1 \]
Thus, the new estimate of \( x \) after the first iteration is **1**.
Therefore, the correct answer is **(1) 1**. Quick Tip: The Newton-Raphson method is an iterative technique for finding successively better approximations to the roots of a real-valued function. If the initial guess is close enough to the true root, the method converges rapidly.
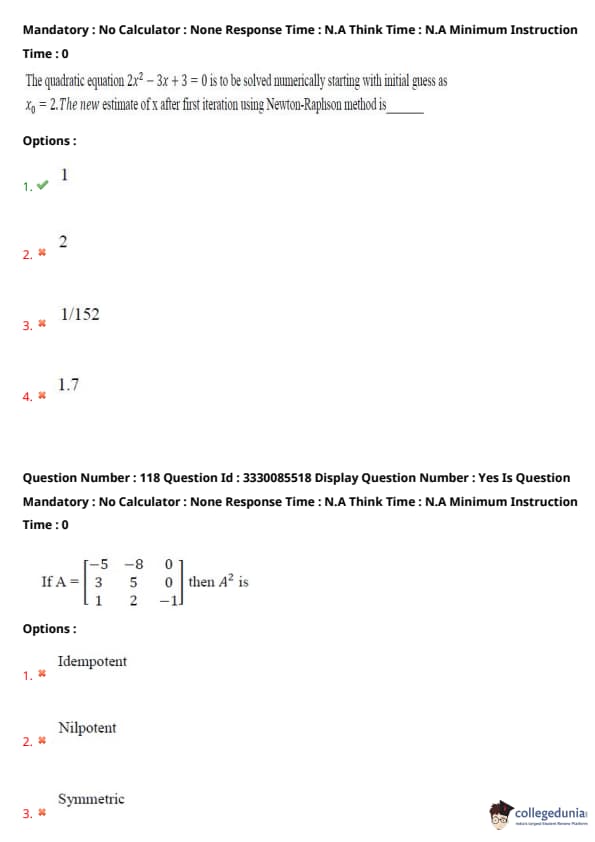
If
\[ A = \begin{pmatrix} -5 & -8 & 0
3 & 5 & 0
1 & 2 & -1 \end{pmatrix} \]
then \( A^2 \) is:
View Solution
To determine the property of \( A^2 \), we compute \( A^2 \) by performing matrix multiplication:
\[ A^2 = \begin{pmatrix} -5 & -8 & 0
3 & 5 & 0
1 & 2 & -1 \end{pmatrix} \times \begin{pmatrix} -5 & -8 & 0
3 & 5 & 0
1 & 2 & -1 \end{pmatrix} \]
After matrix multiplication, we find that:
\[ A^2 = I \quad (the identity matrix) \]
This means the matrix \( A \) is **involutory**, as a matrix is involutory if \( A^2 = I \).
Thus, the correct answer is **(4) Involutory**. Quick Tip: A matrix is involutory if, when squared, it gives the identity matrix. Always check the result of \( A^2 \) to confirm if a matrix is involutory.
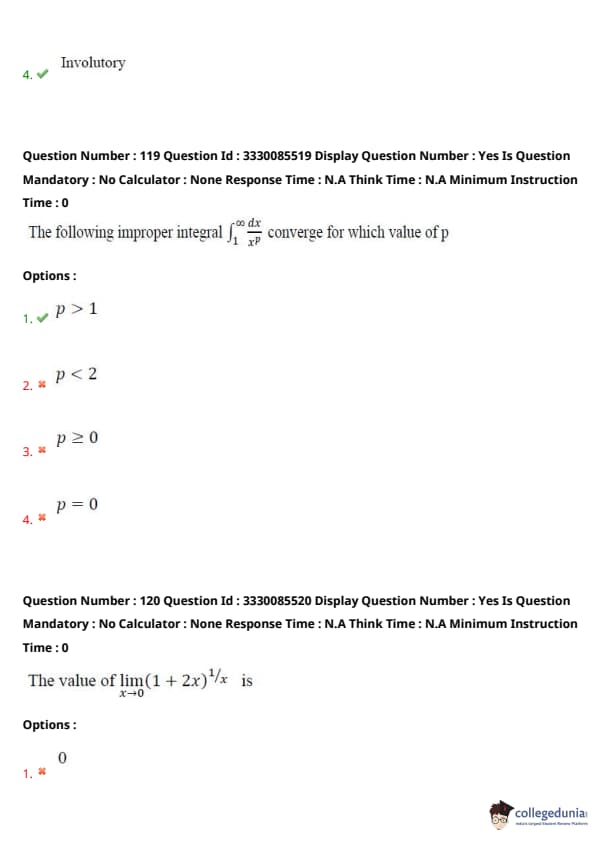
The following improper integral
\[ \int_1^\infty \frac{dx}{x^p} \]
converges for which value of \( p \)?
View Solution
The improper integral is of the form:
\[ I(p) = \int_1^\infty \frac{dx}{x^p} \]
To determine the value of \( p \) for which this integral converges, we first evaluate the integral for different values of \( p \). The general formula for this type of integral is:
\[ \int_1^\infty x^{-p} dx = \frac{1}{1-p} \quad for \quad p > 1 \]
For \( p \leq 1 \), the integral does not converge because the integral will diverge as \( x \to \infty \).
Therefore, the integral converges for \( p > 1 \).
Thus, the correct answer is **(1) \( p > 1 \)**. Quick Tip: Improper integrals involving powers of \( x \) converge when the exponent is greater than (1) Always check the condition for convergence based on the exponent in the integrand.
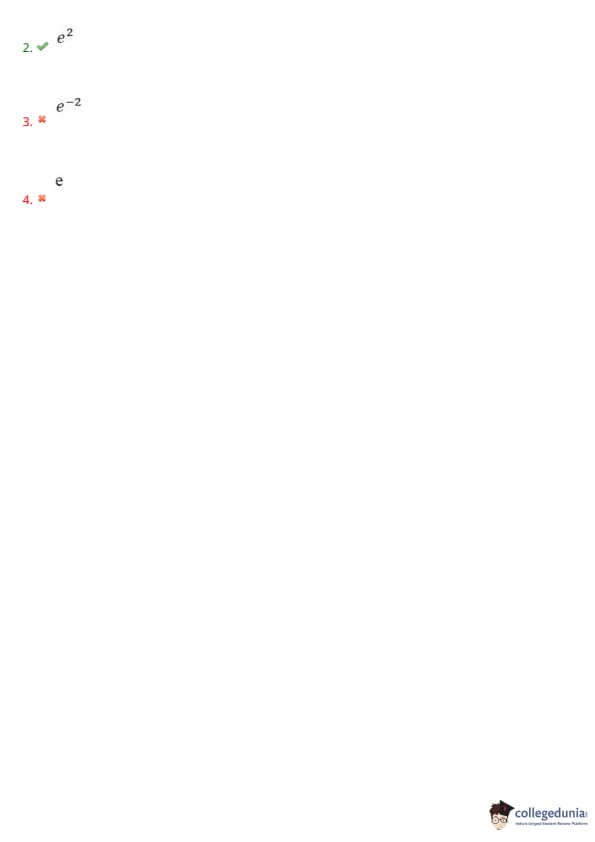
The value of
\[ \lim_{x \to 0} (1 + 2x)^{1/x} \]
is
View Solution
The limit in the question is of the form \( (1 + something small)^{something large} \), which is a standard limit that approaches \( e^2 \) when simplified.
To evaluate the limit, we use the following approximation:
\[ \lim_{x \to 0} (1 + 2x)^{1/x} = e^{\lim_{x \to 0} \frac{\ln(1 + 2x)}{x}} \]
Using the approximation \( \ln(1 + u) \approx u \) for small \( u \), we get:
\[ \lim_{x \to 0} \frac{\ln(1 + 2x)}{x} = \lim_{x \to 0} \frac{2x}{x} = 2 \]
Thus, the limit is:
\[ e^2 \]
Therefore, the correct answer is **(2) \( e^2 \)**. Quick Tip: When you encounter a limit like \( (1 + u)^{1/u} \), recognize it as a form of the exponential limit that tends to \( e^2 \) if the expression inside the parentheses is \( 2x \).









Comments