AP PGECET Question Paper 2025 for Computer Science Engineering is available for download here with answer key and solution PDF. AP PGECET 2025 was conducted from June 6 to June 8 in two shifts.
AP PGECET Question Paper 2025 consists of 120 MCQ-based questions in total carrying 1 mark each to be attempted in the duration of 2 hours.
AP PGECET Computer Science Engineering Question Paper
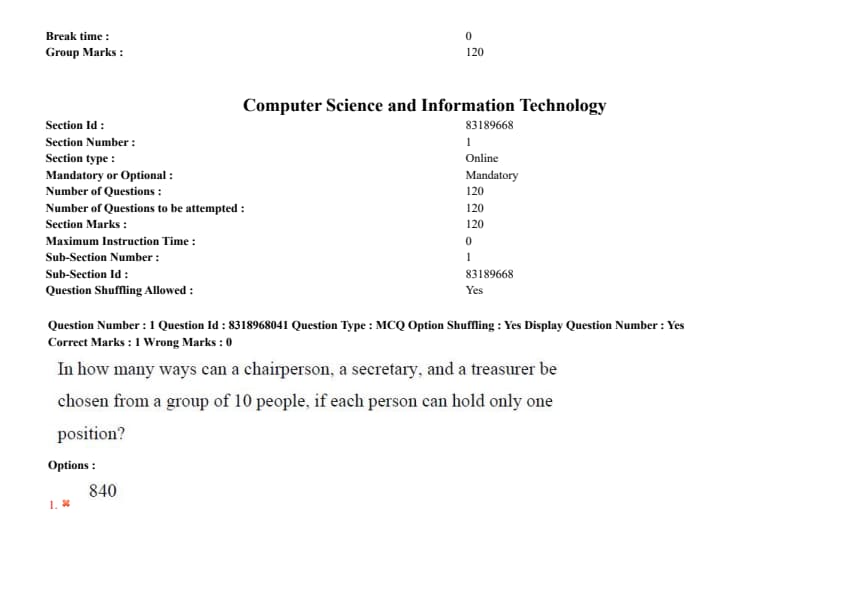
Question 1:
In how many ways can a chairperson, a secretary, and a treasurer be chosen from a group of 10 people, if each person can hold only one position?
- (1) 840
- (2) 5040
- (3) 1240
- (4) 720
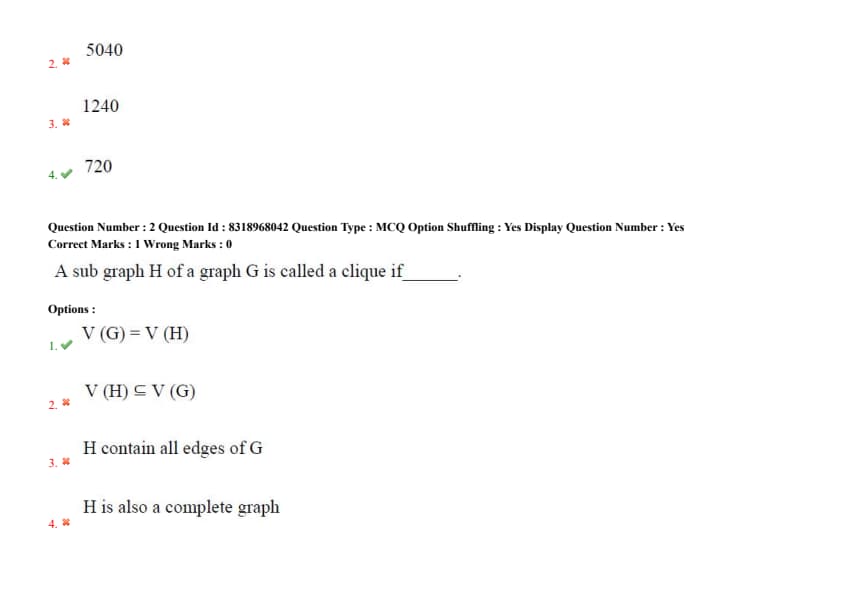
Question 2:
A subgraph H of a graph G is called a clique if ____.
- (1) \( V(G) = V(H) \)
- (2) \( V(H) \subseteq V(G) \)
- (3) \( H \) contains all edges of \( G \)
- (4) \( H \) is also a complete graph
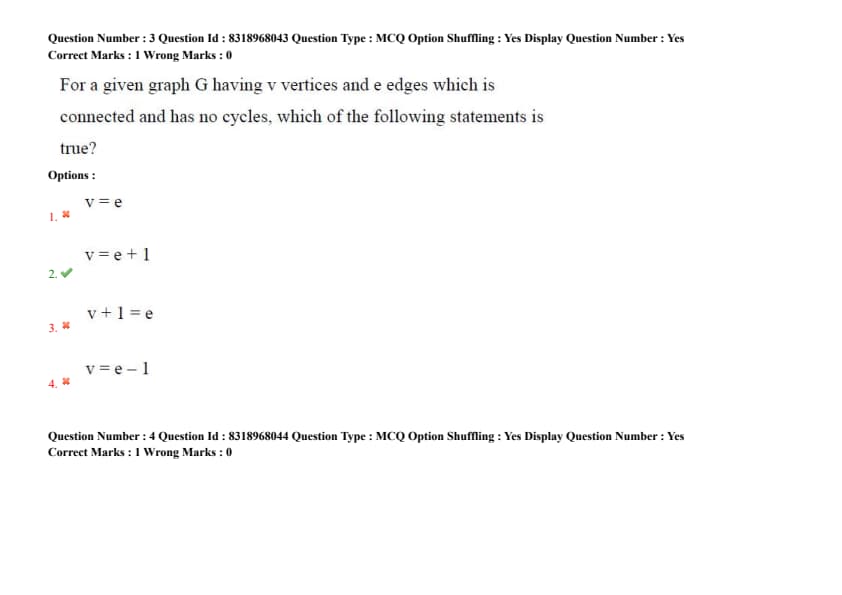
Question 3:
For a given graph G having \( v \) vertices and \( e \) edges which is connected and has no cycles, which of the following statements is true?
- (1) \( v = e \)
- (2) \( v = e + 1 \)
- (3) \( v + 1 = e \)
- (4) \( v = e - 1 \)
Question 4:
Assume G is a simple undirected graph and some vertices of G are of odd degree. Add a node \( v \) to G and make it adjacent to each odd degree vertex of G, then the resultant graph is sure to be ____.
- (1) Euler
- (2) Complete
- (3) Hamiltonian
- (4) Clique
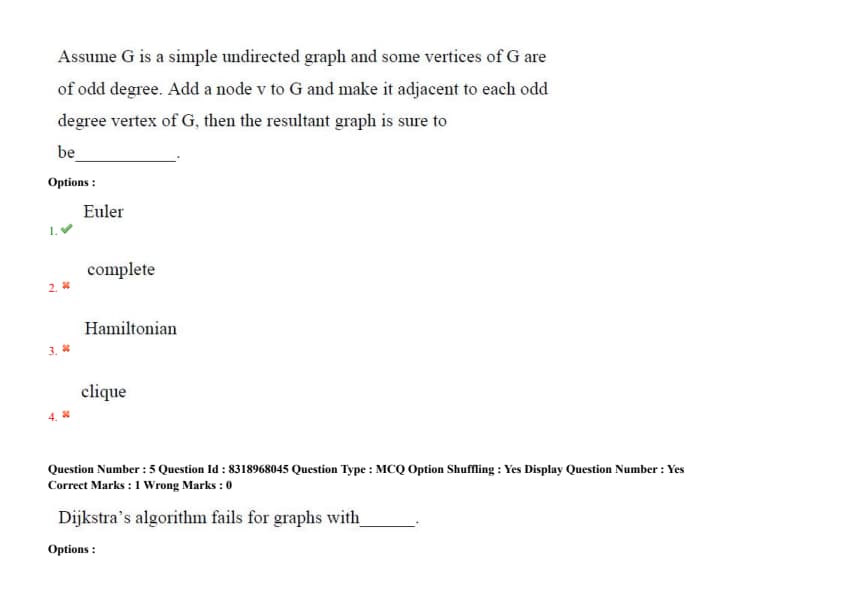
Question 5:
Dijkstra's algorithm fails for graphs with ____.
- (1) Negative weights
- (2) Disconnected components
- (3) Directed edges
- (4) Self-loops
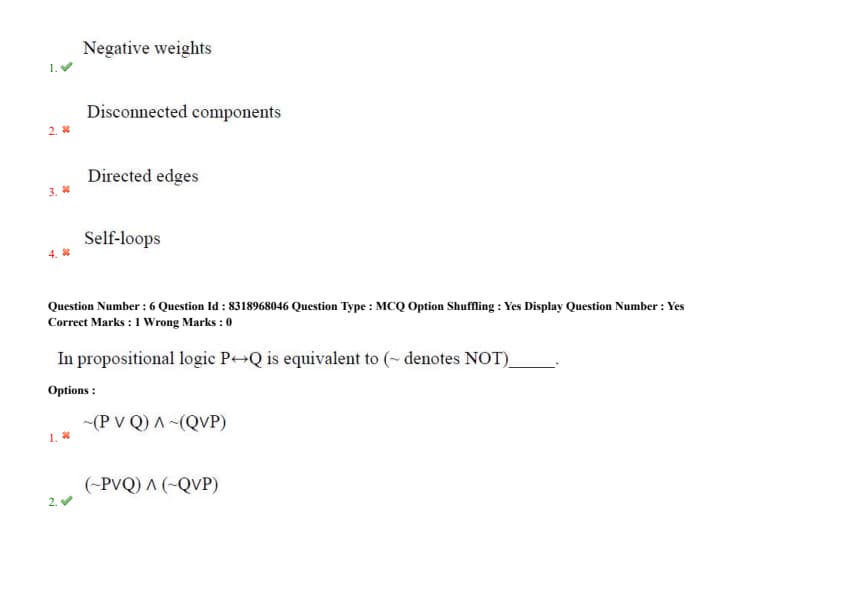
Question 6:
In propositional logic \( P \leftrightarrow Q \) is equivalent to \( \sim \) (denotes NOT) ____.
- (1) \( \sim (P \lor Q) \land \sim (Q \lor P) \)
- (2) \( (\sim P \lor Q) \land (\sim Q \lor P) \)
- (3) \( (P \lor Q) \land (Q \lor P) \)
- (4) \( (\sim P \lor Q) \rightarrow (\sim Q \lor P) \)
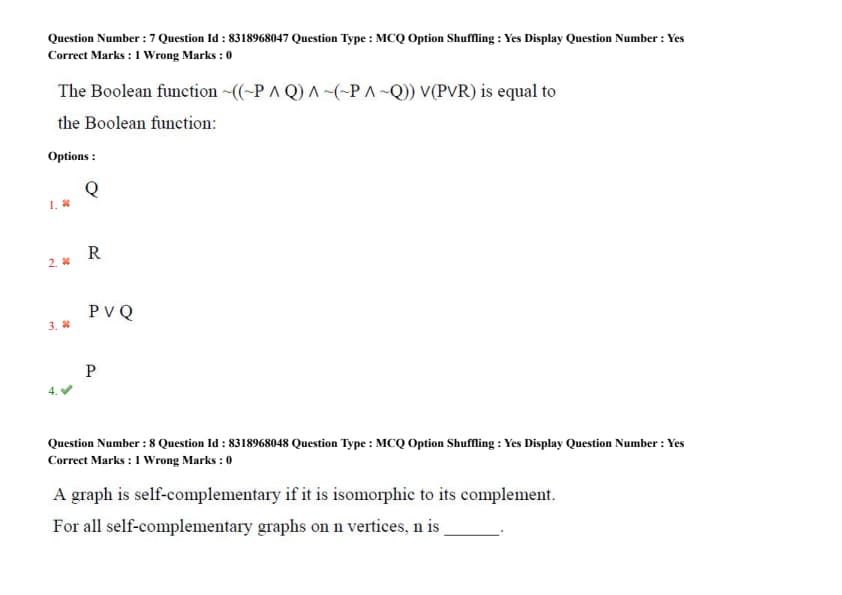
Question 7:
The Boolean function \( \sim (\sim P \land Q) \land (\sim (\sim P \land \sim Q)) \lor (P \lor R) \) is equal to the Boolean function:
- (1) Q
- (2) R
- (3) \( P \lor Q \)
- (4) P
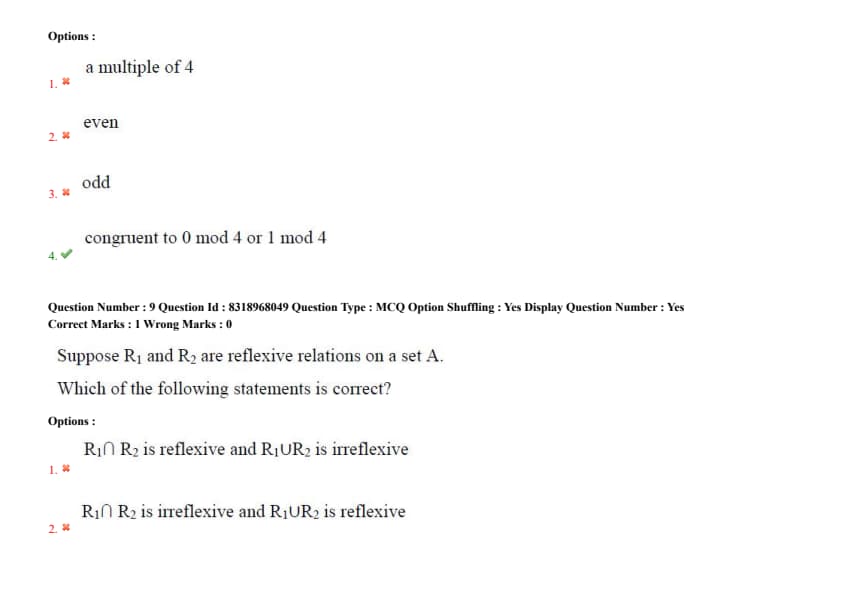
Question 8:
A graph is self-complementary if it is isomorphic to its complement. For all self-complementary graphs on n vertices, \( n \) is ____.
- (1) a multiple of 4
- (2) even
- (3) odd
- (4) congruent to 0 mod 4 or 1 mod 4
Question 9:
Suppose \( R_1 \) and \( R_2 \) are reflexive relations on a set \( A \). Which of the following statements is correct?
- (1) \( R_1 \cap R_2 \) is reflexive and \( R_1 \cup R_2 \) is irreflexive
- (2) \( R_1 \cap R_2 \) is irreflexive and \( R_1 \cup R_2 \) is reflexive
- (3) Both \( R_1 \cap R_2 \) and \( R_1 \cup R_2 \) are irreflexive
- (4) Both \( R_1 \cap R_2 \) and \( R_1 \cup R_2 \) are reflexive
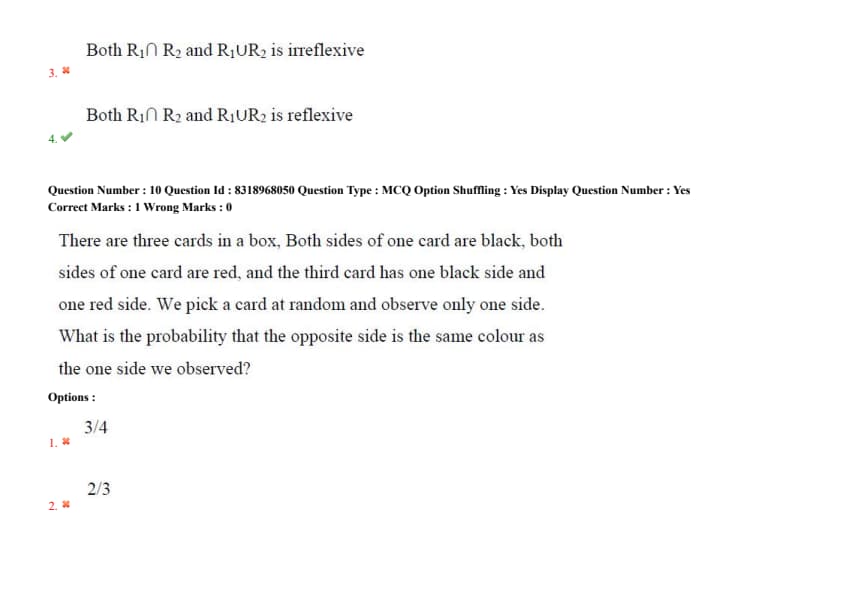
Question 10:
There are three cards in a box. Both sides of one card are black, both sides of one card are red, and the third card has one black side and one red side. We pick a card at random and observe only one side. What is the probability that the opposite side is the same colour as the one side we observed?
- (1) \( \frac{3}{4} \)
- (2) \( \frac{2}{3} \)
- (3) \( \frac{1}{2} \)
- (4) \( \frac{1}{3} \)
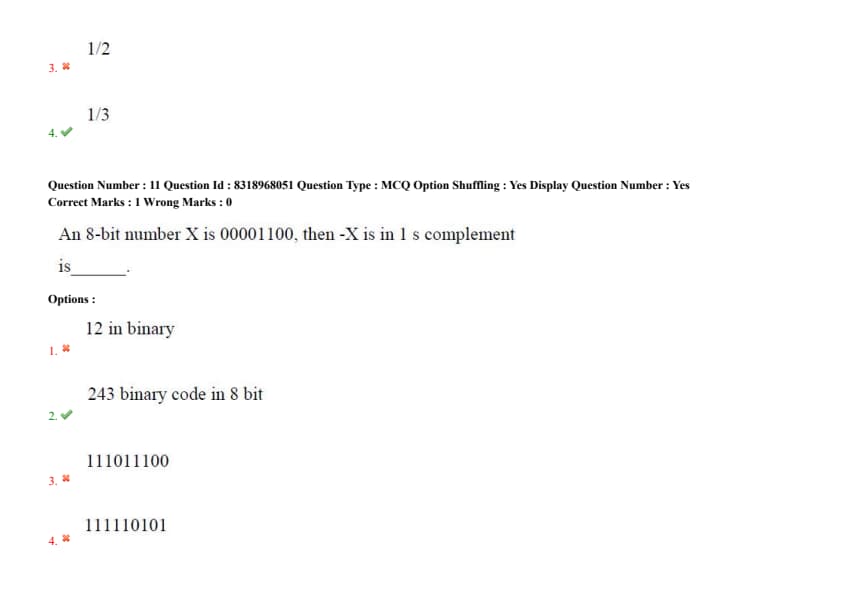
Question 11:
An 8-bit number \( X \) is \( 00001100 \), then \( -X \) is in 1's complement is ____.
- (1) 12 in binary
- (2) 243 binary code in 8 bit
- (3) 11101100
- (4) 11110101
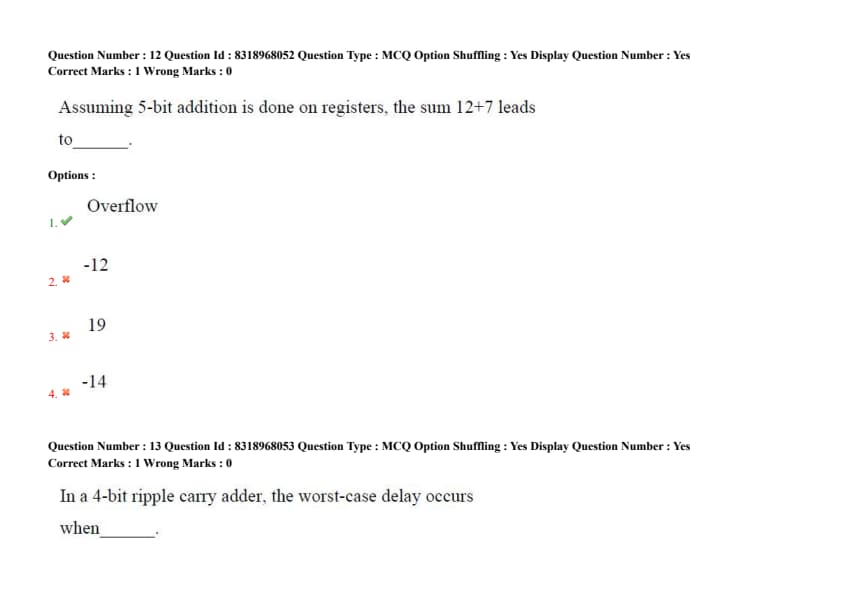
Question 12:
Assuming 5-bit addition is done on registers, the sum \( 12 + 7 \) leads to ____.
- (1) Overflow
- (2) -12
- (3) 19
- (4) -14
Question 13:
In a 4-bit ripple carry adder, the worst-case delay occurs when ____.
- (1) All input bits are 0
- (2) A carry propagates through all full adders
- (3) No carry is generated
- (4) The sum exceeds 15
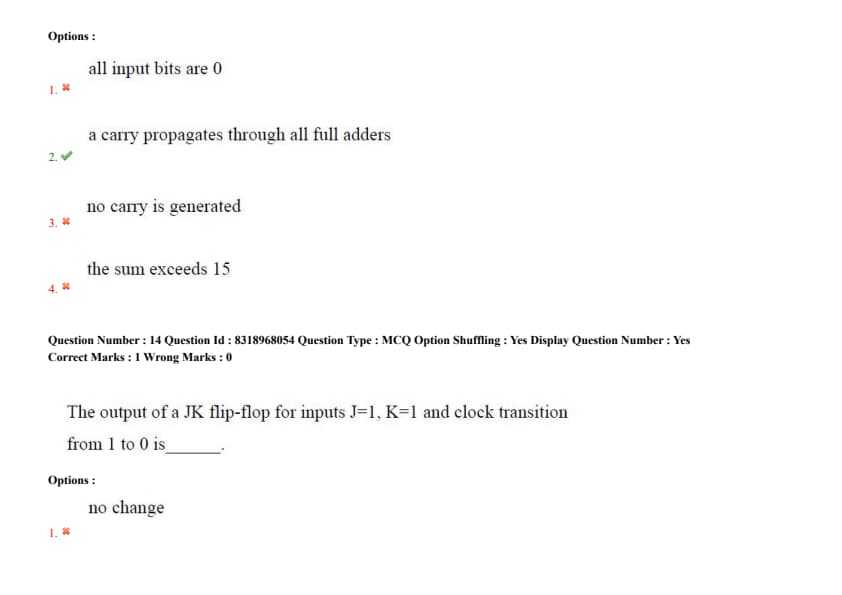
Question 14:
The output of a JK flip-flop for inputs \( J=1, K=1 \) and clock transition from 1 to 0 is ____.
- (1) No change
- (2) Reset
- (3) Toggle
- (4) Set
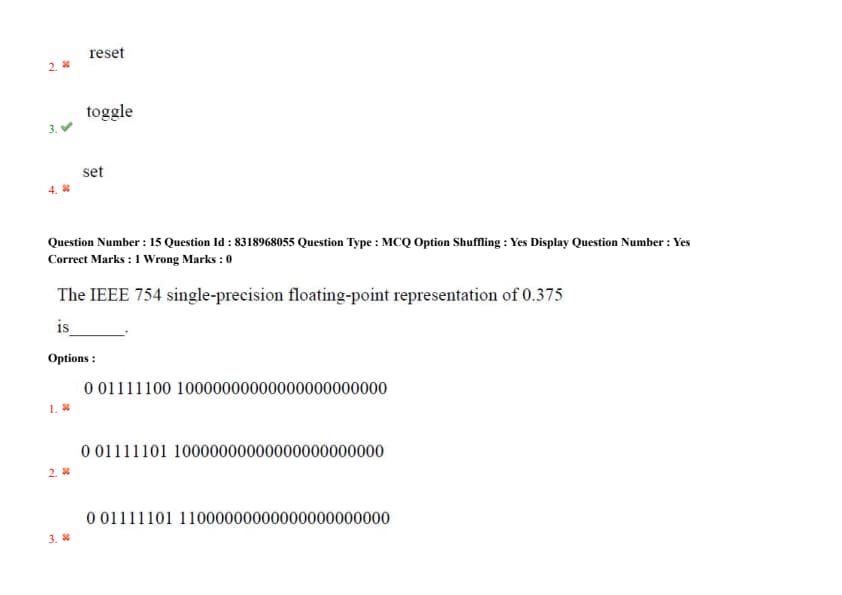
Question 15:
The IEEE 754 single-precision floating-point representation of 0.375 is ____.
- (1) \( 0 0111100 10000000000000000000000 \)
- (2) \( 0 0111101 10000000000000000000000 \)
- (3) \( 0 0111101 11000000000000000000000 \)
- (4) \( 0 0111100 11000000000000000000000 \)
Question 16:
In a hardwired control unit, the sequence of control signals is generated by ____.
- (1) Microprogrammed ROM
- (2) State machine/circuitry
- (3) Operating system
- (4) Interrupt handler
Question 17:
In DMA mode, the CPU is bypassed for data transfer between ____.
- (1) CPU and I/O devices
- (2) Registers and ALU
- (3) Memory and I/O devices
- (4) Cache and secondary storage
Question 18:
A 4-way set-associative cache with 256 blocks divides memory addresses into ____.
- (1) 256 sets
- (2) 64 sets
- (3) 4 sets
- (4) 16 sets
Question 19:
\( AB \oplus (A + B) \) is equivalent to ____.
- (1) \( A^1 B + AB^1 \)
- (2) \( AB + A^1 B^1 \)
- (3) \( A^1 B + A^1 B^1 \)
- (4) \( A + B \)
Question 20:
Which of these flip-flops cannot be used to construct a serial shift register?
- (1) D flip-flop
- (2) SR flip-flop
- (3) T flip-flop
- (4) JK flip-flop
Question 21:
How many AND gates are required to realize \( Y = CD + EF + G \)?
Question 22:
The purpose of an interrupt vector table is to ____.
- (1) Store CPU registers during context switch
- (2) Map interrupt requests to service routine addresses
- (3) Hold page tables for virtual memory
- (4) Cache frequently used instructions
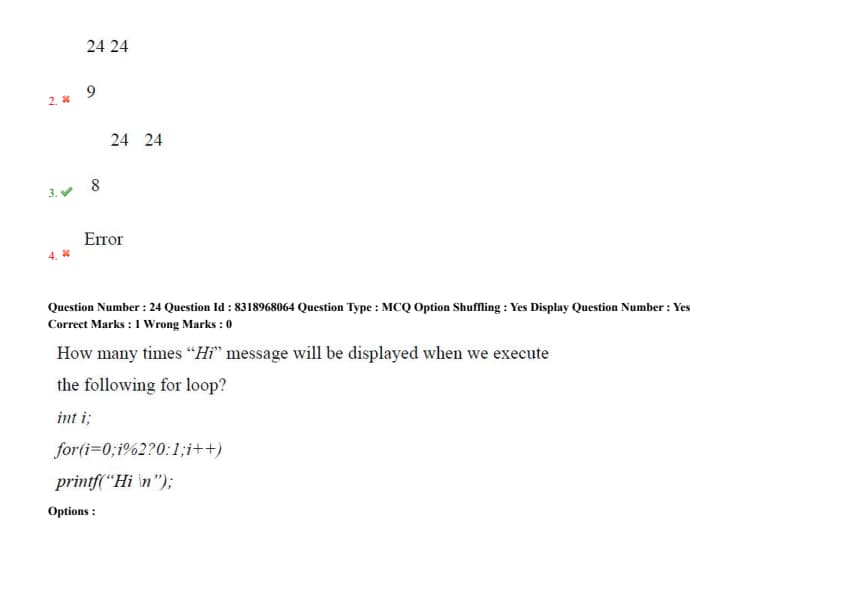
Question 23:
What is the output of the following code fragment?
\texttt{int x = 24;
\texttt{printf("%d\n", x); printf("%3d %3d\n", x, x);
- (1) 24 24
10
- (2) 24 24
9
- (3) 24 24
8
- (4) error
Question 24:
How many times “Hi” message will be displayed when we execute the following for loop?
\texttt{int i;
\texttt{for(i=0;i%2==0;i++)
\texttt{printf("Hi \textbackslash n");
Question 25:
If one wants to add and delete elements quickly without reshuffling the rest, then which data structure suits the best?
- (1) Linked list
- (2) Tree
- (3) B-Tree
- (4) Array
Question 26:
The height of a binary tree with 31 nodes (assuming no single-child nodes) is ____.
Question 27:
In a max-heap, the largest element is always located at the ____.
- (1) Leftmost leaf
- (2) Rightmost leaf
- (3) Root node
- (4) Middle of the heap
Question 28:
The recurrence T(n) = 2T(n/2) + n has a solution of ____.
- (1) O(n)
- (2) O(nlogn)
- (3) O(n²)
- (4) O(logn)
Question 29:
What is the time complexity to insert an element at the beginning of a dynamic array?
- (1) O(1)
- (2) O(n)
- (3) O(nlogn)
- (4) O(logn)
Question 30:
The inorder traversal of a BST gives elements in ____.
- (1) Level order
- (2) Ascending order
- (3) Descending order
- (4) Random order
Question 31:
A threaded binary tree is a binary tree in which every node that does not have right child has a thread to its ____.
- (1) Pre-order successor
- (2) In-order successor
- (3) In-order predecessor
- (4) Post-order successor
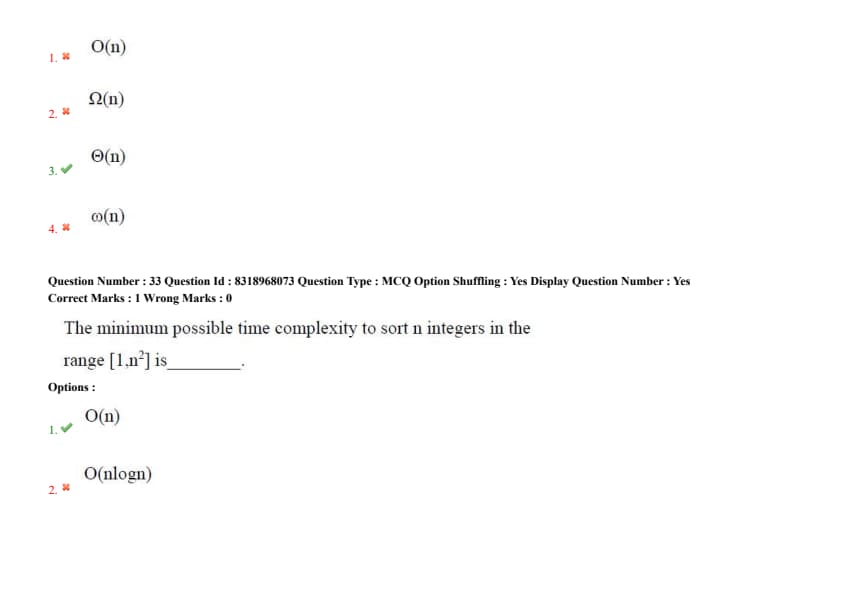
Question 32:
Which notation represents the tightest upper bound of an algorithm’s running time?
- (1) O(n)
- (2) \(\Omega(n)\)
- (3) \(\Theta(n)\)
- (4) \(\omega(n)\)
Question 33:
The minimum possible time complexity to sort \(n\) integers in the range [1, \(n^2\)] is ____ .
- (1) O(n)
- (2) O(n\log n)
- (3) O(n\(^2\))
- (4) O(\(\log n\))
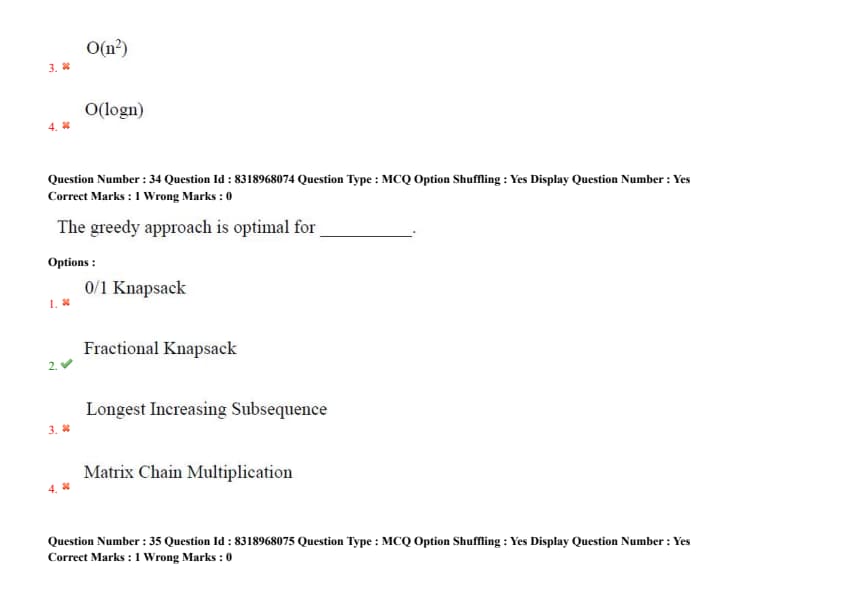
Question 34:
The greedy approach is optimal for ____ .
- (1) 0/1 Knapsack
- (2) Fractional Knapsack
- (3) Longest Increasing Subsequence
- (4) Matrix Chain Multiplication
Question 35:
Best case complexity of insertion sorting is ____ .
- (1) O(n)
- (2) O(n\log n)
- (3) O(n\(^2\))
- (4) O(\(\log n\))
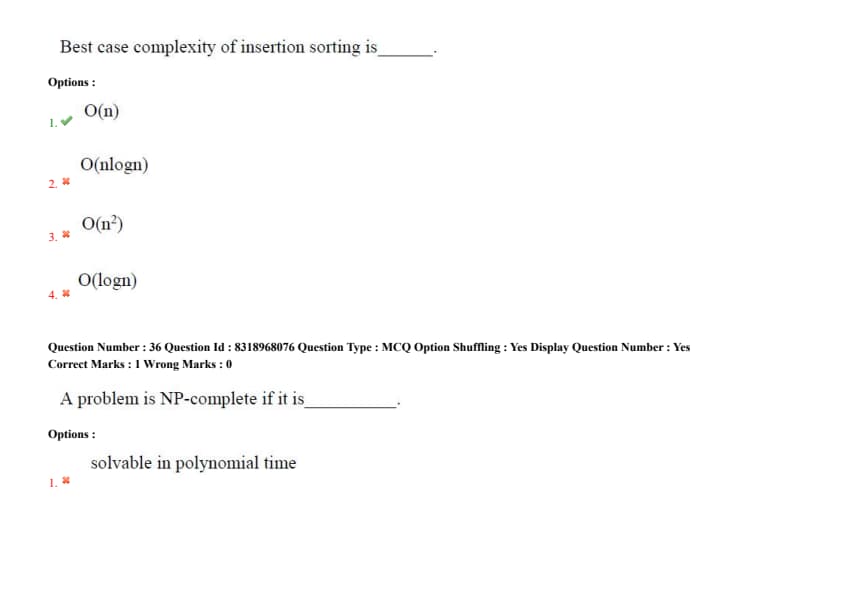
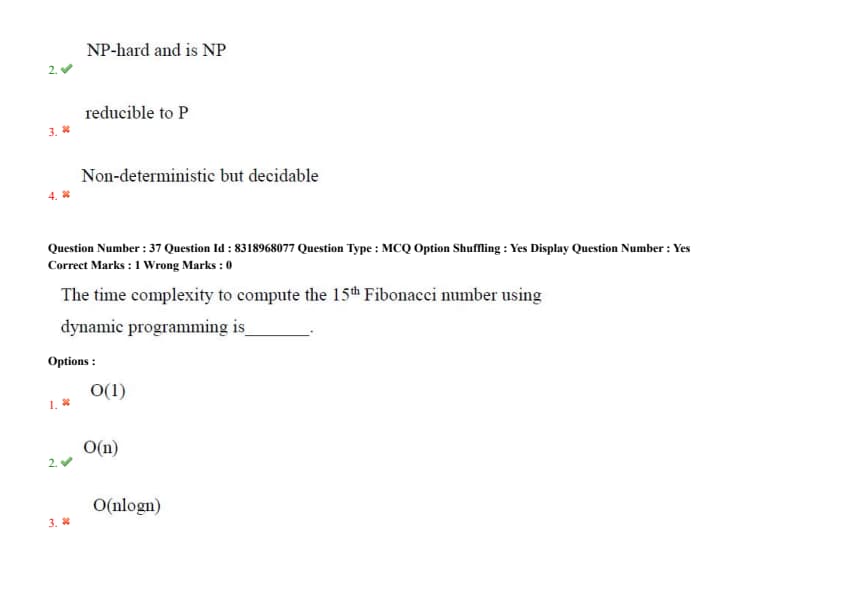
Question 36:
A problem is NP-complete if it is ____ .
- (1) Solvable in polynomial time
- (2) NP-hard and is NP
- (3) Reducible to P
- (4) Non-deterministic but decidable
Question 37:
The time complexity to compute the 15\(^th\) Fibonacci number using dynamic programming is ____ .
- (1) O(1)
- (2) O(n)
- (3) O(n\log n)
- (4) O(\(\log n\))
Question 38:
One way to build a heap is to start at the end of the array (the leaves) and push each new value up to the root. Its time complexity is ____ .
- (1) O(n)
- (2) O(\log n)
- (3) O(n \log n)
- (4) O(n\(^2\) \log n)
Question 39:
If the recursive call keeps calculating the same things over and over again, we can use ____ which stores partial results already calculated and to be used again.
- (1) Divide and conquer algorithm
- (2) Recursive
- (3) Dynamic Programming
- (4) Greedy method
Question 40:
The ____ process updates the costs of all the vertices \(V\), connected to a vertex \(U\), if we could improve the best estimate of the shortest path to \(V\) by including \((U,V)\) in the path to \(V\).
- (1) Relaxation
- (2) Improvement
- (3) Shortening
- (4) Costing
Question 41:
The minimum number of states in a DFA accepting \( L = \{ w | w ends with 01 \} \) over \( \Sigma = \{0, 1\} \) is ____ .
Question 42:
The language \( L = \{M | M halts on all inputs\} \) is ____ .
- (1) Decidable
- (2) Undecidable but recognizable
- (3) Not recognizable
- (4) Regular
Question 43:
Inherited attributes in SDTs are used for ____ .
- (1) Passing information up the parse tree
- (2) Passing information down the parse tree
- (3) Storing symbol table entries
- (4) Generating target code
Question 44:
The output of a syntax-directed translation scheme is ____ .
- (1) Abstract Syntax Tree
- (2) Three Address Code
- (3) Postfix Notation
- (4) Depends on the SDT rules
Question 45:
Subset Construction method refers to ____ .
- (1) Conversion of NFA to DFA
- (2) DFA minimization
- (3) Eliminating Null references
- (4) DFA to NFA
Question 46:
The maximum number of transitions which can be performed over a state in a DFA? \( \Sigma = \{a, b, c\} \)
Question 47:
Which of the following is a regular language?
- (1) A string whose length is a sequence of prime numbers
- (2) A string with substring ww\(^f\)
- (3) A palindrome
- (4) A string with even number of zero’s
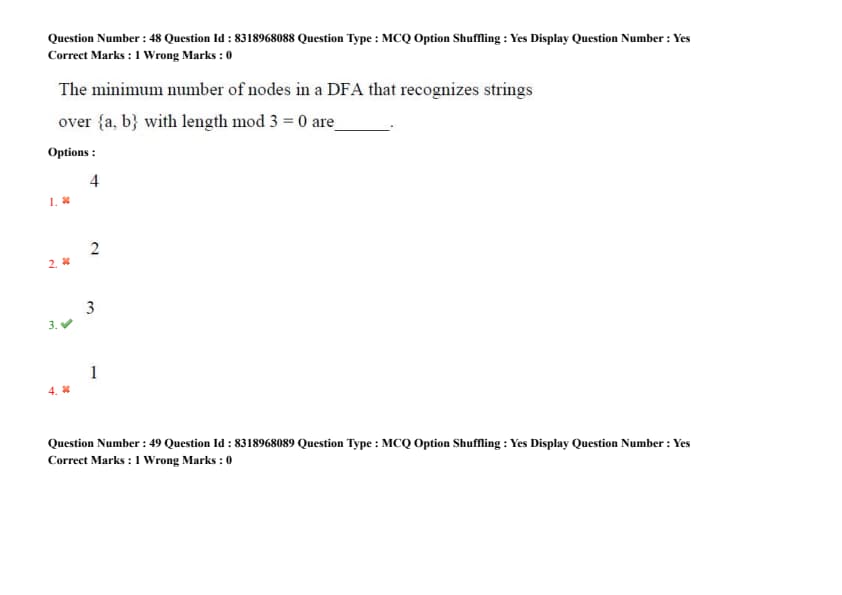
Question 48:
The minimum number of nodes in a DFA that recognizes strings over \( \{a, b\} \) with length mod 3 = 0 are ____ .
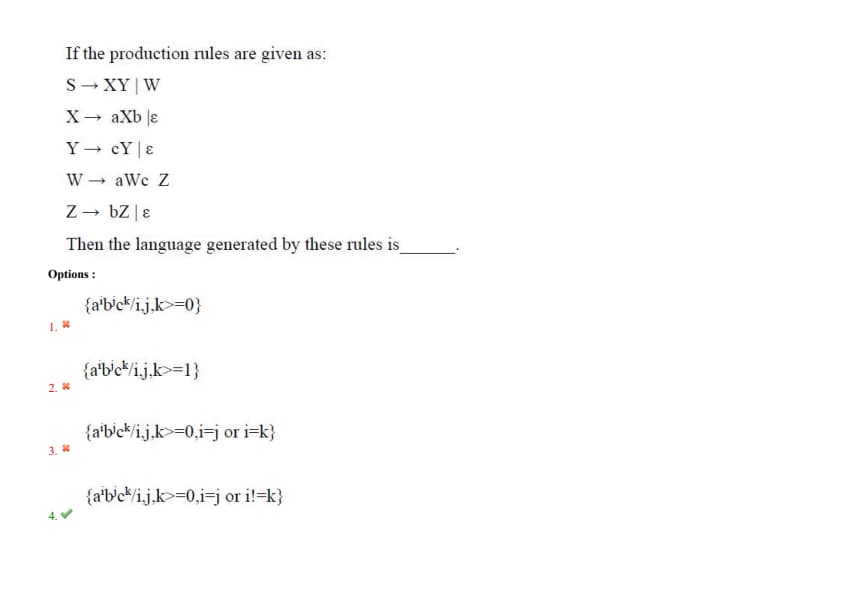
Question 49:
If the production rules are given as:
\( S \to XY | W \)
\( X \to aXb | \epsilon \)
\( Y \to cY | \epsilon \)
\( W \to aWc | bZ | \epsilon \)
\( Z \to bZ | \epsilon \)
Then the language generated by these rules is ____ .
- (1) \( \{ a^i b^i \mid i \geq 0 \} \)
- (2) \( \{ a^i b^i \mid i \geq 1 \} \)
- (3) \( \{ a^i b^j c^k \mid i \geq 0, j \geq 0, k \geq 0 \} \)
- (4) \( \{ a^i b^j c^k \mid i = j or i = k \} \)
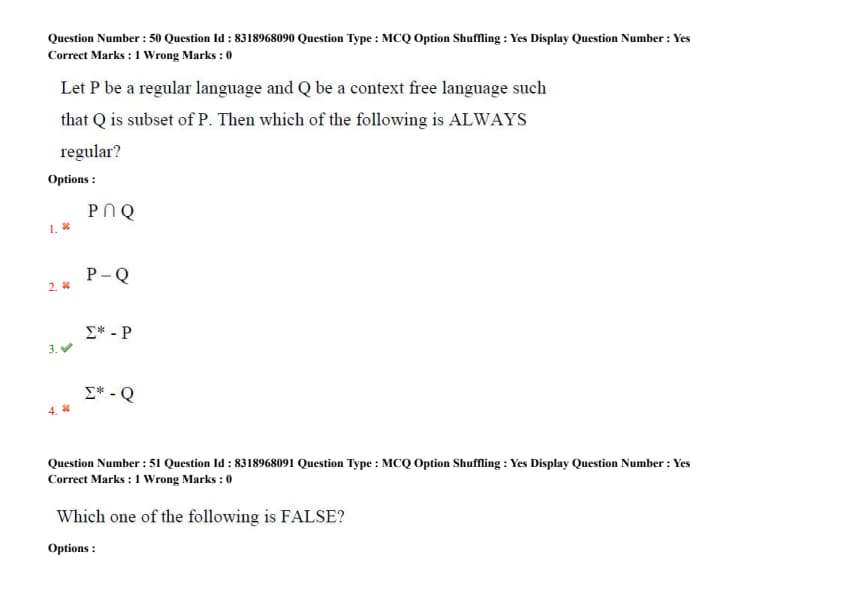
Question 50:
Let \( P \) be a regular language and \( Q \) be a context free language such that \( Q \) is a subset of \( P \). Then which of the following is ALWAYS regular?
- (1) \( P \cap Q \)
- (2) \( P - Q \)
- (3) \( \Sigma^* - P \)
- (4) \( \Sigma^* - Q \)
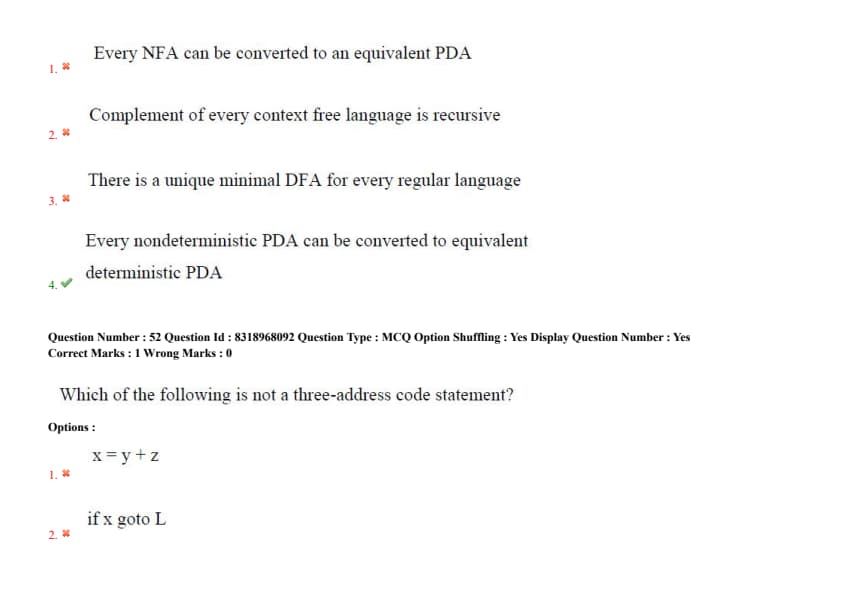
Question 51:
Which of the following is FALSE?
- (1) Every NFA can be converted to an equivalent PDA
- (2) Complement of every context free language is recursive
- (3) There is a unique minimal DFA for every regular language
- (4) Every nondeterministic PDA can be converted to an equivalent deterministic PDA
Question 52:
Which of the following is not a three-address code statement?
- (1) \( x = y + z \)
- (2) if \( x \) goto L
- (3) \( x = *y \)
- (4) \( x = y ** z \)
Question 53:
Which of the following is not shared among threads in the same process?
- (1) Heap memory
- (2) Stack
- (3) File Descriptors
- (4) Code section
Question 54:
The primary advantage of user-level threads over kernel-level threads is ____ .
- (1) Lower context-switch overhead
- (2) Better parallelism on multicore CPUs
- (3) No need for synchronization
- (4) Higher priority scheduling
Question 55:
A program uses environment variables to ____ .
- (1) Store data between login sessions
- (2) Pass configuration settings to other programs
- (3) Store data persistently
- (4) Pass data to the operating system
Question 56:
Which is not a CPU scheduling criterion?
- (1) CPU utilization
- (2) Reliability
- (3) Response time
- (4) Waiting time
Question 57:
Among priority inversion between two processes, one with high priority and other with low priority that share a critical section will cause which of the following problem?
- (1) High priority process executes before low priority process and finishes faster than it should.
- (2) Low priority process executes before high priority process and finishes faster than it should.
- (3) High priority process waits for low priority process to finish, but the low priority process never gets scheduled.
- (4) Low priority process changes priority temporarily to the priority of the high priority process.
Question 58:
A currently running process can be put on a ready queue or one of the I/O queues by each of the following except ____ .
- (1) The process issued an I/O request
- (2) The process did an illegal memory access
- (3) There was an interrupt
- (4) The process issued a system call
Question 59:
Which of the following component of program state is shared across threads in a multithreaded process?
- (1) Registers
- (2) Auto variables
- (3) Heap memory
- (4) Stack memory
Question 60:
Which of the following frees the CPU from having to deal with transfer of memory to or from I/O device?
- (1) Interrupts
- (2) Direct Memory Access
- (3) Buffer cache
- (4) Device Driver
Question 61:
In FCFS, I/O bound processes may have to wait long in the ready queue waiting for a CPU bound job to finish. This is known as ____ .
- (1) Aging
- (2) Convoy effect
- (3) Priority inversion
- (4) Belady's anomaly
Question 62:
In general, there will be ____ inodes than directories in Unix File system.
- (1) Zero
- (2) Less
- (3) Same
- (4) More
Question 63:
To ensure that the ____ condition never occurs in the system, we must guarantee that, whenever a process requests a resource, it does not have any other resource.
- (1) Mutual exclusion
- (2) No-preemption
- (3) Circular wait
- (4) Hold and wait
Question 64:
A ____ architecture assigns only a few essential functions to the kernel, including address spaces, Interprocess communication (IPC), and basic scheduling.
- (1) Monolithic kernel
- (2) Micro kernel
- (3) Macro kernel
- (4) Mini kernel
Question 65:
Among the four criteria for synchronization mechanism, which of the two criteria are mandatory?
- (1) Mutual exclusion and Progress
- (2) Progress and Architectural neutral
- (3) Bounded wait and mutual exclusion
- (4) Bounded wait and progress
Question 66:
Which SQL operation is not part of the ACID properties?
- (1) COMMIT
- (2) ROLLBACK
- (3) CREATE INDEX
- (4) SAVEPOINT
Question 67:
A B+ tree is preferred over a B-tree for databases because ____ .
- (1) It supports range queries efficiently
- (2) It has a smaller node size
- (3) It allows faster insertion/deletion
- (4) It uses less disk space
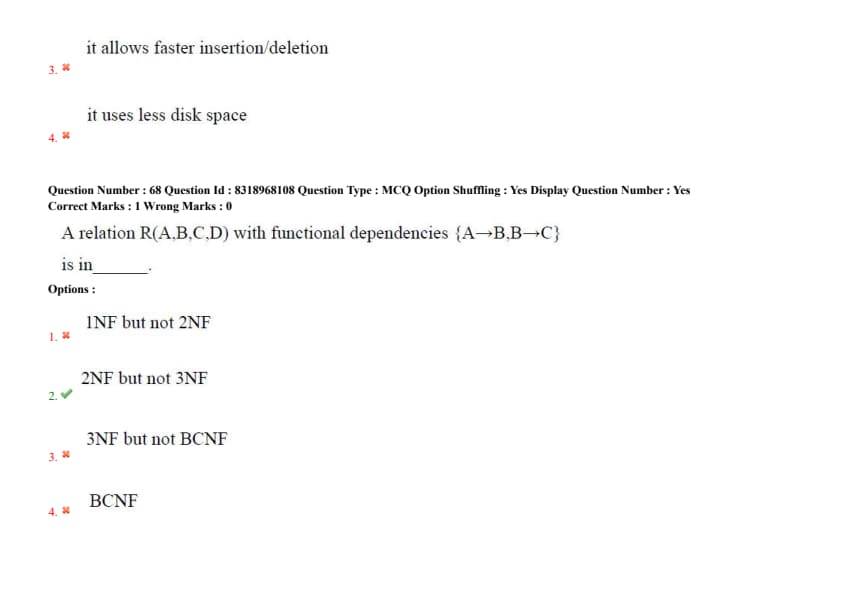
Question 68:
A relation \(R(A,B,C,D)\) with functional dependencies \{A→B, B→C\ is in ____ .
- (1) 1NF but not 2NF
- (2) 2NF but not 3NF
- (3) 3NF but not BCNF
- (4) BCNF
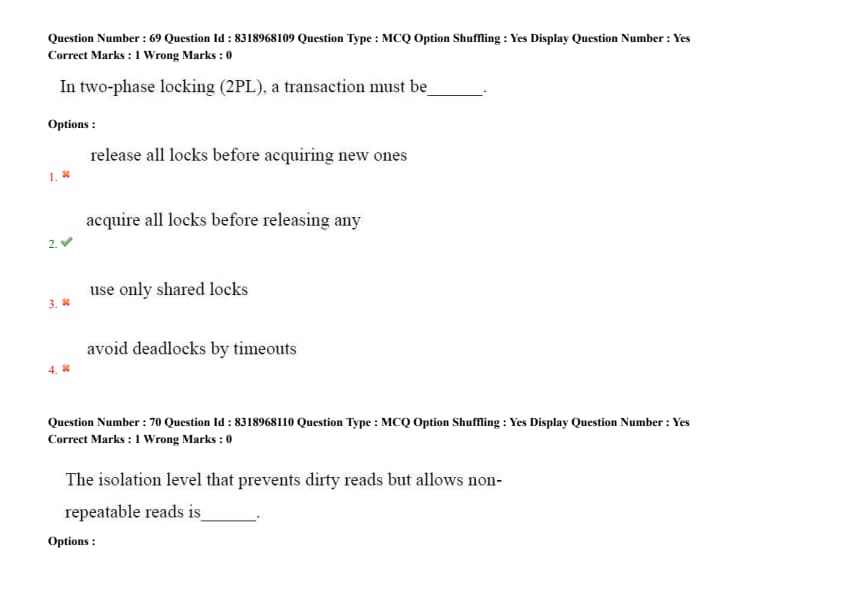
Question 69:
In two-phase locking (2PL), a transaction must be ____ .
- (1) Release all locks before acquiring new ones
- (2) Acquire all locks before releasing any
- (3) Use only shared locks
- (4) Avoid deadlocks by timeouts
Question 70:
The isolation level that prevents dirty reads but allows non-repeatable reads is ____ .
- (1) read uncommitted
- (2) read committed
- (3) repeatable read
- (4) serializable
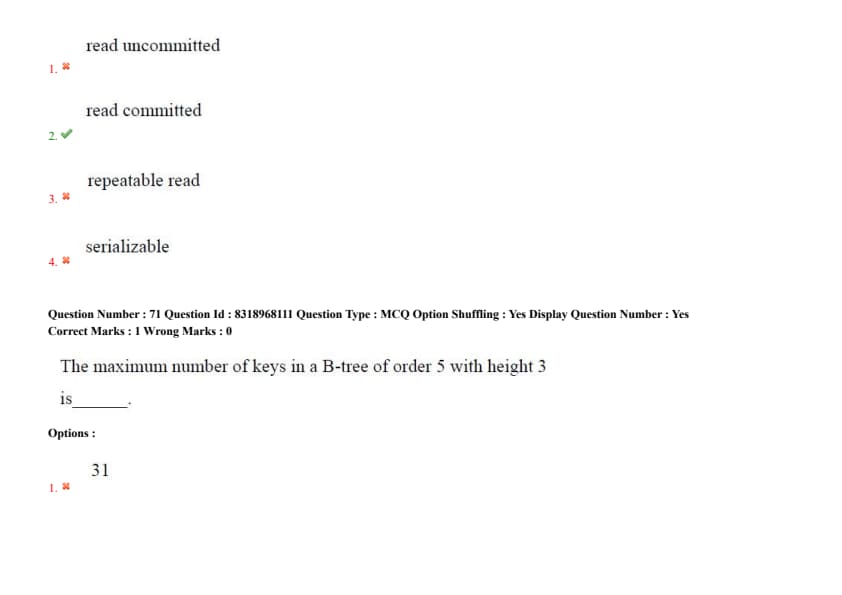
Question 71:
The maximum number of keys in a B-tree of order 5 with height 3 is ____ .
- (1) 31
- (2) 156
- (3) 624
- (4) 3125
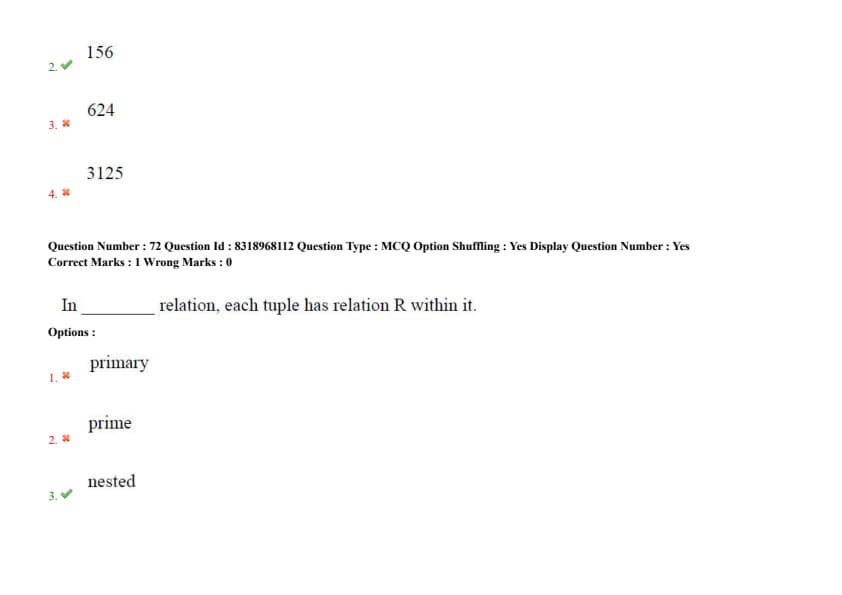
Question 72:
In ____ relation, each tuple has relation R within it.
- (1) primary
- (2) prime
- (3) nested
- (4) atomic
Question 73:
The rule which states that addition of same attributes to the right side and left side will result in other valid dependency is classified as ____ .
- (1) Augmentation rule
- (2) Inference rule
- (3) Referential rule
- (4) Reflexive rule
Question 74:
The separation of the data definition from program is known as ____ .
- (1) Data dictionary
- (2) Data independence
- (3) Data integrity
- (4) Referential integrity
Question 75:
Which is the candidate key for the relation R(ABCDE) with functional dependencies F={A→BC, B→D, CD→E, E→A}?
Question 76:
Natural Join can also be termed as ____ .
- (1) combination of Union and Cartesian Product
- (2) combination of Selection and Cartesian Product
- (3) combination of Projection and Cartesian Product
- (4) combination of Projection and Union
Question 77:
If A \(\to\) B has trivial functional dependency, then _____.
- (1) B is a subset of A
- (2) A is a subset of B
- (3) A is a subset of A'
- (4) B is a subset of B'
Question 78:
Which of the following commands is used to delete all rows and free up space from a table?
- (1) Drop
- (2) Delete
- (3) Truncate
- (4) Alter
Question 79:
____ uses Quantifiers that can be either Existential (*) or Universal (V).
- (1) Domain Relational Calculus
- (2) Tuple Relational Calculus
- (3) Distributed Relational Calculus
- (4) NoSQL
Question 80:
The database design that consists of multiple tables that are linked together through matching data stored in each table is called a _____.
- (1) Relational database
- (2) Network database
- (3) Object oriented database
- (4) Hierarchical database
Question 81:
The incremental model of software development is _____.
- (1) a reasonable approach when requirements are well defined
- (2) a good approach when a working core product is required quickly
- (3) the best approach to use for projects with large development teams
- (4) a revolutionary model that is not used for commercial products
Question 82:
The cyclomatic complexity metric provides the designer with information regarding the number of _____.
- (1) cycles in the program
- (2) errors in the program
- (3) independent logic paths in the program
- (4) statements in the program
Question 83:
In the spiral model of software development, the primary determinant in selecting activities in each iteration is _____.
- (1) iteration size
- (2) cost
- (3) risk
- (4) adopted process such as rational unified process or extreme programming
Question 84:
The optimizer that explores the space of all query-evaluation plans is called _____.
- (1) cost-based
- (2) plan-based
- (3) estimate-based
- (4) count-based
Question 85:
The term that optimizes subexpressions shared by different expressions in a program is called _____.
- (1) multiple subexpression elimination
- (2) common subexpression elimination
- (3) parametric subexpression elimination
- (4) shared subexpression elimination
Question 86:
Frequency of failure and network recovery time after a failure are measures of the _____ of a network.
- (1) performance
- (2) reliability
- (3) security
- (4) feasibility
Question 87:
A Gantt chart is least useful for tracking _____.
- (1) task dependencies
- (2) resource allocation
- (3) critical path
- (4) code complexity
Question 88:
Which phase of the SDLC typically consumes the most resources?
- (1) Requirements gathering
- (2) Testing
- (3) Maintenance
- (4) Coding
Question 89:
Regression testing is performed to ensure that _____.
- (1) new code doesn't break existing functionality
- (2) all paths are covered
- (3) users accept the system
- (4) compliance with laws
Question 90:
The COCOMO model estimates _____.
- (1) project risk
- (2) software cost
- (3) team productivity
- (4) user satisfaction
Question 91:
At which OSI layer does MAC address filtering occur?
- (1) Network
- (2) Data Link
- (3) Transport
- (4) Physical
Question 92:
Token Ring networks avoid collisions by _____.
- (1) CSMA/CD
- (2) Token passing
- (3) Exponential backoff
- (4) Priority queuing
Question 93:
Which routing algorithm guarantees shortest paths even with negative edge weights?
- (1) Dijkstra's
- (2) Bellman-Ford
- (3) Link-State
- (4) OSPF
Question 94:
A TCP header includes all except _____.
- (1) Sequence number
- (2) Checksum
- (3) TTL
- (4) Window size
Question 95:
The three-way handshake in TCP ensures _____.
- (1) Encryption setup
- (2) Synchronized sequence numbers
- (3) QoS negotiation
- (4) Multicast membership
Question 96:
An IPv4 datagram with header length=5 and total length=400 bytes carries _____.
- (1) 380 bytes payload
- (2) 400 bytes payload
- (3) 20 bytes header
- (4) 320 bytes payload
Question 97:
Which protocol uses port 53 by default?
- (1) HTTP
- (2) FTP
- (3) DNS
- (4) SMTP
Question 98:
A switch differs from a hub because, it _____.
- (1) operates at Layer 1
- (2) broadcasts all frames
- (3) uses MAC tables for forwarding
- (4) only supports half-duplex
Question 99:
Digital signatures provide _____.
- (1) confidentiality
- (2) non-repudiation
- (3) key exchange
- (4) firewall bypass
Question 100:
In asynchronous transmission, the gap time between bytes is _____.
- (1) fixed
- (2) variable
- (3) a function of the data rate
- (4) zero
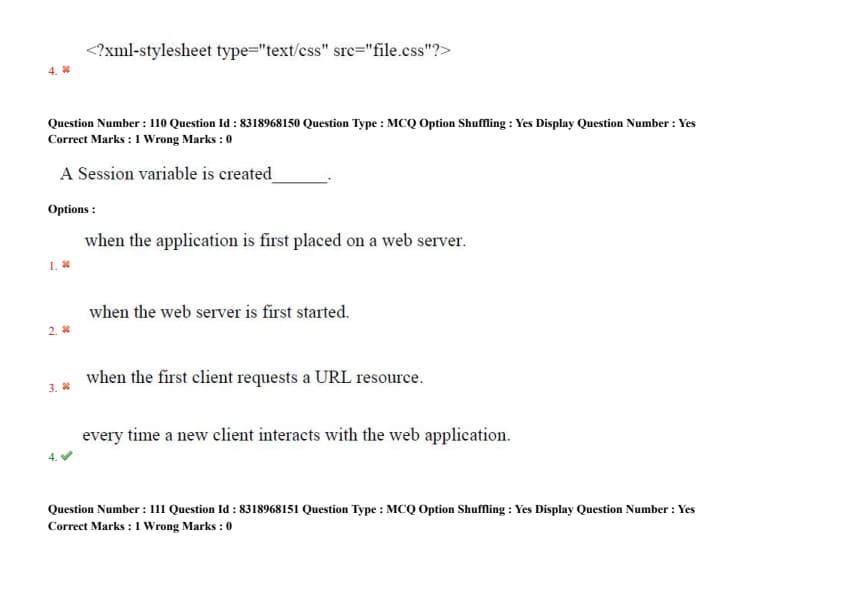
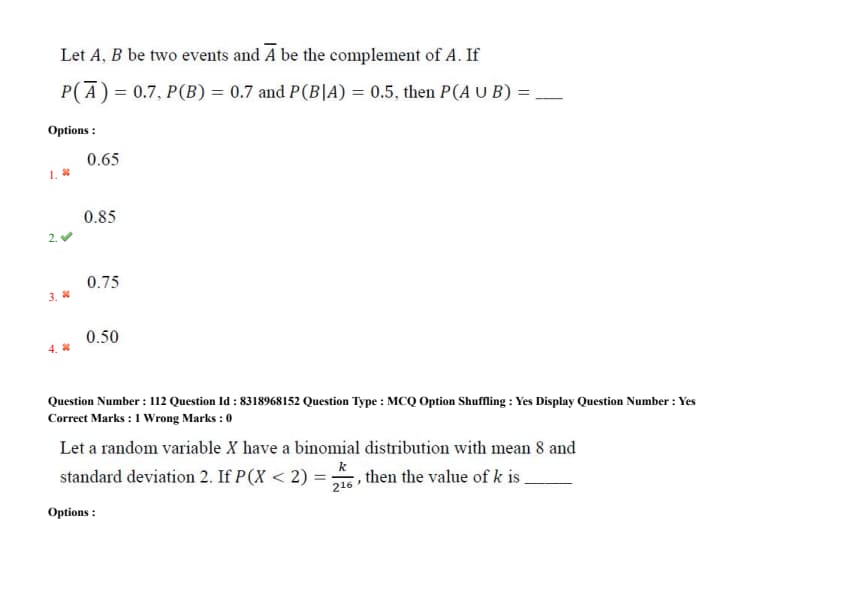
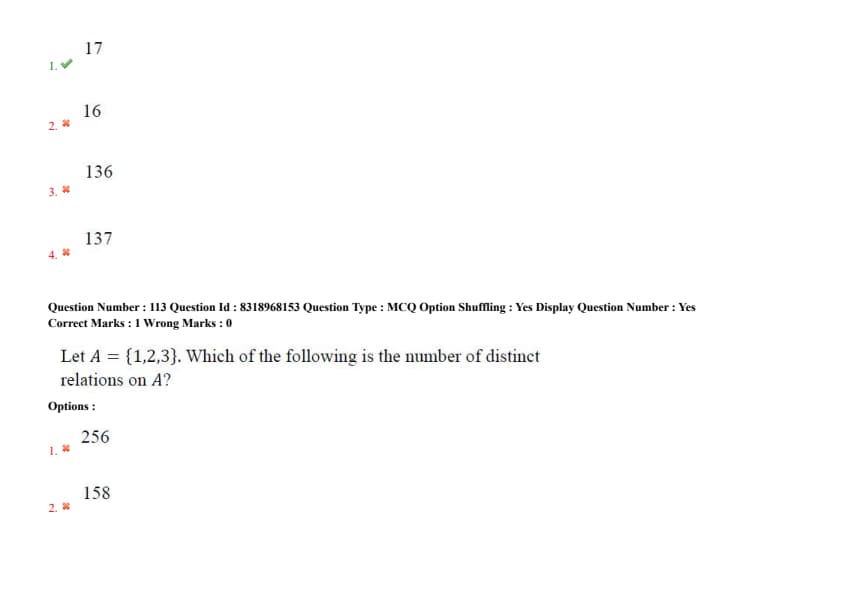
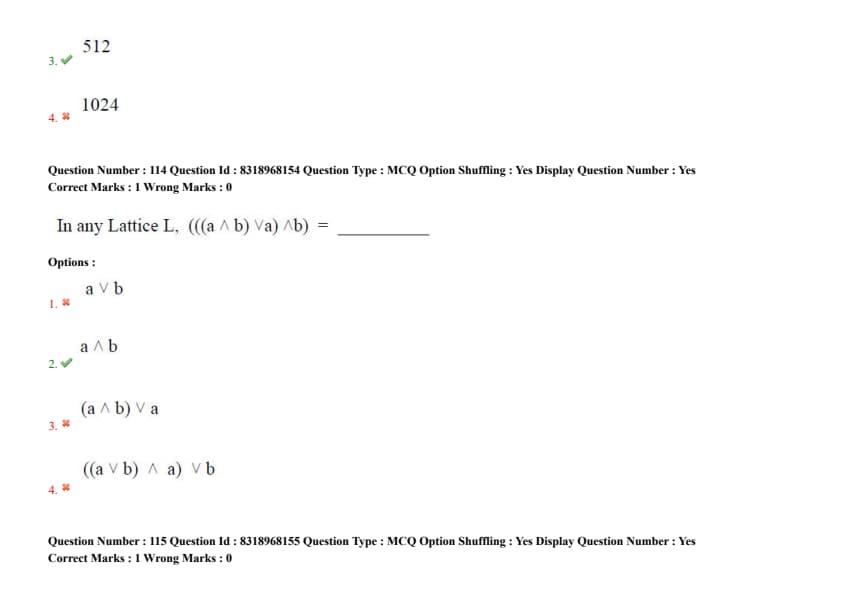
Question 101:
In Java, when we implement an interface method, it must be declared as _____.
- (1) private
- (2) protected
- (3) public
- (4) friend
Question 102:
Which of the following control fields in TCP header is used to specify whether the sender has no more data to transport?
- (1) FIN
- (2) RST
- (3) SYN
- (4) PSH
Question 103:
In XML, DOCTYPE declaration specifies to include a reference to _____ file.
- (1) document type declaration
- (2) document type definition
- (3) document type language
- (4) document transfer definition
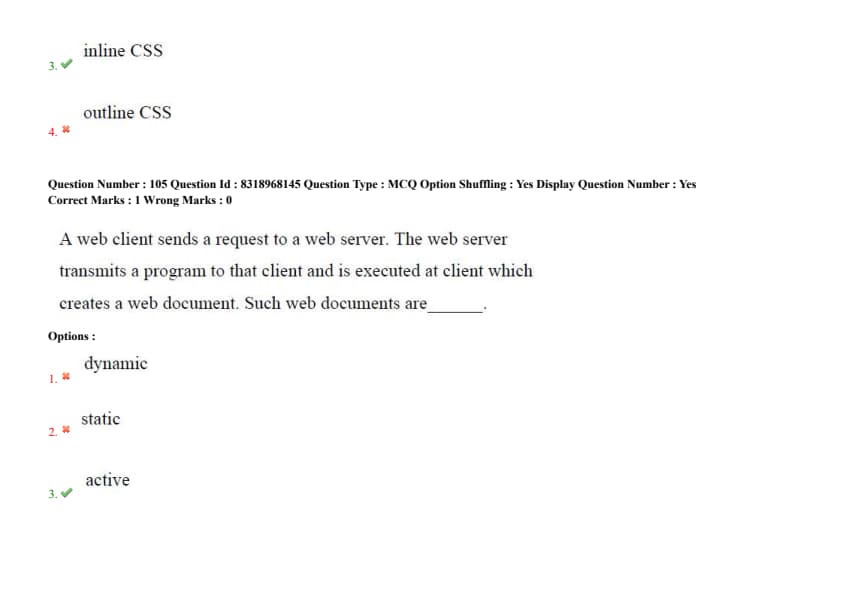
Question 104:
The CSS used inside HTML elements alongside style attribute is called _____.
- (1) external CSS
- (2) internal CSS
- (3) inline CSS
- (4) outline CSS
Question 105:
A web client sends a request to a web server. The web server transmits a program to that client and is executed at client which creates a web document. Such web documents are _____.
- (1) dynamic
- (2) static
- (3) active
- (4) passive
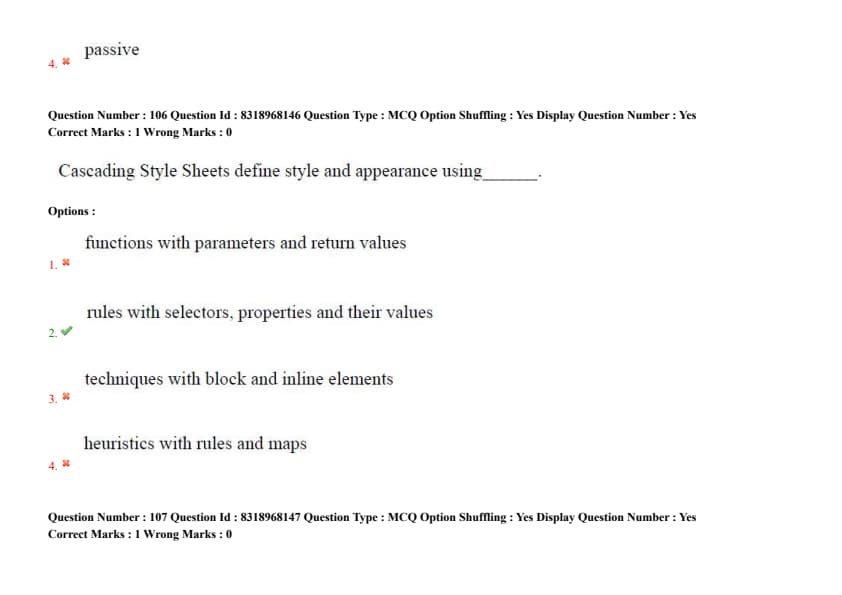
Question 106:
Cascading Style Sheets define style and appearance using _____.
- (1) functions with parameters and return values
- (2) rules with selectors, properties and their values
- (3) techniques with block and inline elements
- (4) heuristics with rules and maps
Question 107:
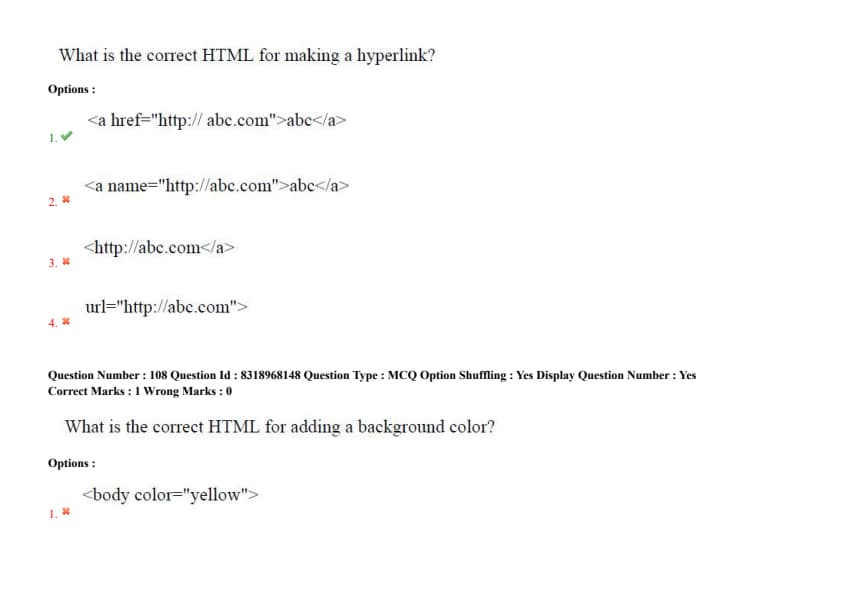
What is the correct HTML for making a hyperlink?
- (1) \texttt{abc}
- (2) \texttt{abc}
- (3) \texttt{}
- (4) \texttt{url="http://abc.com">}
}}}
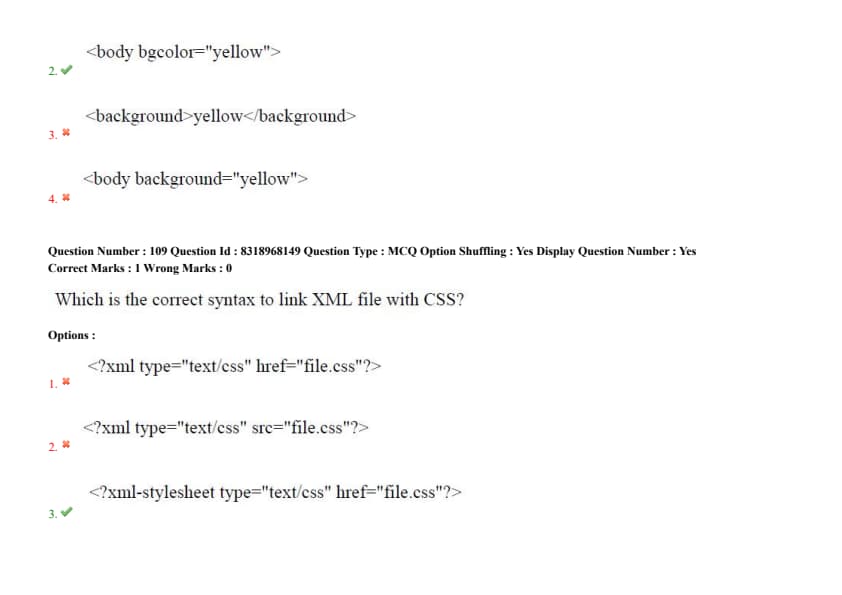
View Solution
In HTML, the background color of a page can be set using the \texttt{bgcolor attribute within the \texttt{
tag. It is not recommended to use inline styling for this; CSS is preferred for modern web development.
Quick Tip: While \texttt{bgcolor} is still supported in HTML, it is recommended to use CSS for styling in modern web development.







Comments